What Is Cybersecurity
Cybersecurity is the practice of protecting computers, networks, software, and data from digital attacks, damage, or unauthorized access. It involves using technologies, processes, and security measures to defend against cyber threats such as hacking, phishing, malware, and data breaches. The main goal of cybersecurity is to ensure the confidentiality, integrity, and availability (CIA) of information.
Cybersecurity includes different areas such as network security, which protects internal networks from intruders; application security, which secures software and programs from vulnerabilities; information security, which safeguards sensitive data; and cloud security, which protects data stored online. It also involves practices like using strong passwords, encryption, firewalls, antivirus software, and regular system updates.
Organizations like the National Institute of Standards and Technology provide cybersecurity frameworks and guidelines to help businesses manage risks. As technology continues to grow, cybersecurity has become essential for individuals, businesses, and governments to protect against increasing cyber threats and ensure safe digital communication.
Why is cybersecurity important
Cybersecurity is important because it protects sensitive information, systems, and networks from cyber threats and unauthorized access. In today’s digital world, individuals, businesses, and governments store large amounts of personal, financial, and confidential data online. Without proper cybersecurity measures, this data can be stolen, misused, or destroyed by hackers.
Strong cybersecurity helps prevent identity theft, financial loss, data breaches, and damage to an organization’s reputation. For businesses, a cyber attack can disrupt operations, cause loss of customer trust, and lead to legal consequences. For individuals, weak security can result in stolen passwords, bank fraud, or privacy violations.
Cybersecurity is also essential for protecting critical infrastructure such as healthcare, banking, and energy systems. Organizations like the Cybersecurity and Infrastructure Security Agency work to safeguard national infrastructure from cyber threats. As cyber attacks continue to grow in frequency and sophistication, cybersecurity plays a vital role in ensuring safe communication, secure transactions, and overall digital safety.
Cyber threat examples
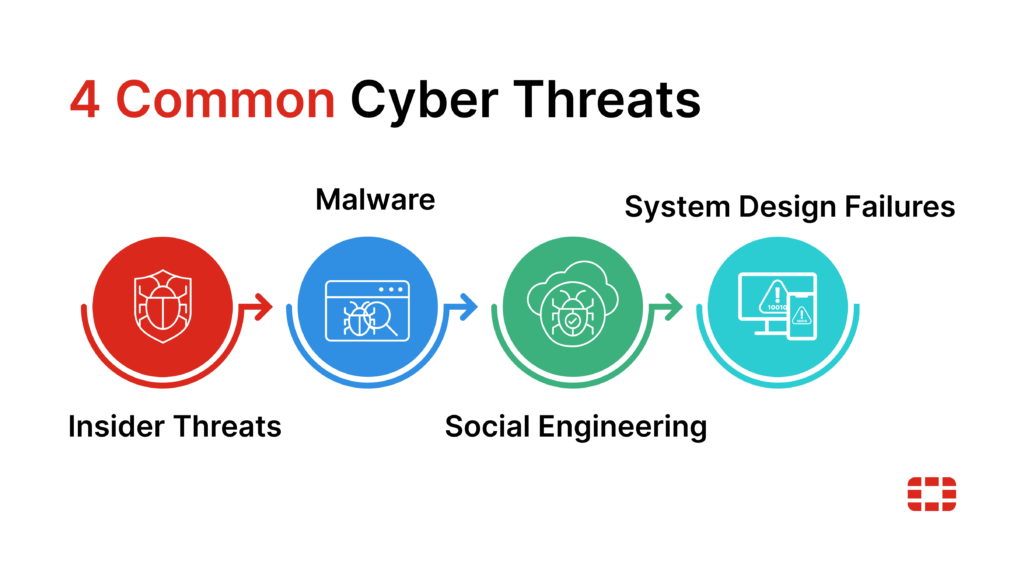
Insider threats
Not all cybersecurity incidents originate externally. Insider threats occur when individuals within an organization — employees, contractors, partners, etc. — intentionally or unintentionally compromise security. These events are especially dangerous because insiders often have legitimate and privileged access to sensitive information, making it easier to cause harm or expose data.
Insider threats come in two forms:
- Malicious insiders: These individuals intentionally exploit their access to steal data, sabotage systems, or leak confidential information. Motivations can range from financial gain to revenge or corporate espionage. For example, a disgruntled employee with access to critical systems might delete valuable data or sell trade secrets to competitors.
- Unintentional insiders: These threats arise when employees unknowingly create security risks through careless actions, such as falling victim to phishing attacks, using weak passwords, or mishandling sensitive data.
Strong cybersecurity helps prevent identity theft, financial loss, data breaches, and damage to an organization’s reputation. For businesses, a cyber attack can disrupt operations, cause loss of customer trust, and lead to legal consequences. For individuals, weak security can result in stolen passwords, bank fraud, or privacy violations.
Cybersecurity is also essential for protecting critical infrastructure such as healthcare, banking, and energy systems. Organizations like the Cybersecurity and Infrastructure Security Agency work to safeguard national infrastructure from cyber threats. As cyber attacks continue to grow in frequency and sophistication, cybersecurity plays a vital role in ensuring safe communication, secure transactions, and overall digital safety.
Malware
Malware, or malicious software, refers to any software program designed to harm computer systems, networks, or users. It can infect devices, steal data, or disrupt operations, making it one of the most common and impactful cyber threats.
Although it comes in many forms, malware typically falls into the following categories:
- Viruses: A virus attaches itself to a legitimate file or program and spreads to other systems when the infected file is shared or executed. Once activated, viruses can corrupt files, steal data, or damage systems.
- Trojan horses: Disguised as legitimate software, trojans trick users into downloading and installing them. Once inside the system, they create backdoors for attackers to steal data, install more malware, or take control of the device.
- Worms: Unlike viruses, worms can replicate themselves and spread across networks without any human interaction. Worms often exploit vulnerabilities in operating systems, quickly infecting large numbers of devices and causing widespread damage.
- Botnet: A botnet is a network of compromised devices, often controlled remotely by cybercriminals. These “bots” can launch large-scale strikes such as distributed denial-of-service (DDoS) attacks, which overwhelm systems with illegitimate traffic to take them offline.
- Ransomware: This form of malware encrypts the victim’s files or locks them out of information systems, demanding payment in exchange for their safe return. Ransomware attacks can severely disrupt operations by holding critical data hostage until the ransom is paid.
Social engineering
Social engineering is a type of cyberattack that relies on human interaction to manipulate individuals into revealing sensitive information or performing actions that compromise security. Rather than exploiting software vulnerabilities, social engineering preys on human psychology, making it one of the most challenging threats to prevent.
Frequent examples include:
- Phishing: Attackers send deceptive emails or messages that appear legitimate, tricking individuals into clicking malicious links, providing login credentials, or downloading malware. Phishing is one of the most widespread social engineering tactics, often targeting employees with privileged accounts.
- Fraud: This involves tricking individuals or organizations into sharing confidential information or making unauthorized payments. Attackers may pose as trusted entities, such as vendors or executives, to deceive their targets.
- Scams: These attacks involve convincing individuals to provide sensitive information or transfer money under false pretenses, often by creating a sense of urgency or fear. Common scams include fake tech support calls or lottery scams.
- Influence campaigns: Attackers manipulate public opinion or decision-making processes through misinformation or disinformation, often using social media. These campaigns can destabilize businesses or even governments by spreading false information to large audiences.
System design failure
A system design failure is a security flaw within a computer system or application that a bad actor exploits to gain access. For instance, coding errors and misconfigurations during the development process may leave gaps in an application’s security posture. If the application isn’t updated after deployment, hackers could leverage these open vulnerabilities to their advantage.
One of the most common ways cybercriminals do so is through a structured query language (SQL) injection. SQL is a standard language used to query databases. Bad actors try to insert an SQL query into regular input or form fields, passing it to the application’s underlying database. This can lead to unauthorized access to sensitive data, corruption, or even a complete database takeover.
Building Blocks of a Comprehensive Cybersecurity Strategy

Cybersecurity isn’t a singular solution but rather a convergence of multiple approaches. They work together in concert to protect users, systems, networks, and data from all angles, minimizing risk exposure.
By combining these layers of protection, businesses can create a more resilient defense against cyber threats of all shapes and sizes.
1. Network security
Network security safeguards communication infrastructure, including devices, hardware, software, and communication protocols. It protects data integrity, confidentiality, and availability as information travels over a network and between network-accessible assets, such as a computer and an application server.
Network security also encompasses a broad collection of technologies, policies, people, and procedures. These focus primarily on preventing known threats from infiltrating the communication infrastructure.
For example, firewalls filter incoming and outgoing traffic, acting as a first line of defense by identifying familiar attack types, suspicious activity, or unauthorized access attempts based on pre-defined rules. The idea is that firewalls already know what to expect and have the capability to block these threats before they can cause harm.
However, network security tools must also include an element of detection. Firewalls and other network security solutions must be able to identify unfamiliar or new threats and, through integration with other systems, respond appropriately to mitigate the risk. Within this context, understanding the distinction between network security vs cyber security provides clarity on where each discipline contributes to an organization’s broader security strategy. To strengthen this posture, organizations also need continuous visibility into emerging network security threats and vulnerabilities, ensuring protections evolve alongside new attack techniques.
2. Information security
Information security, or InfoSec, is the practice of protecting information. It refers to the tools and processes for preventing, detecting, and remediating threats to sensitive information, whether digitized or not.
InfoSec is closely related to data security — a subset that specifically protects digitized data stored in systems and databases or transmitted across networks. Both disciplines share three primary objectives:
- Confidentiality: Ensuring confidential information remains a secret.
- Integrity: Protecting information from being altered, manipulated, or deleted.
- Availability: Making information readily accessible to those who need it.
Therefore, information and data security solutions safeguard against unauthorized access, modification, and disruption. A key aspect of both disciplines is the need to scrutinize information, allowing organizations to classify it by criticality and adjust policies accordingly.
For example, data loss prevention (DLP) tools automatically discover and classify data as it’s created. They also monitor, detect, and prevent unauthorized data sharing or extraction, ensuring valuable information remains secure within the organization.
3. Cloud security
Cloud security refers to the technologies, policies, and procedures that protect data, applications, and services hosted in private and public cloud environments. It ensures sensitive information is safe from data breaches and other vulnerabilities, whether stored in public, private, or hybrid clouds. Cloud security solutions are often versions of on-premises solutions that are specifically for the cloud. As such, cloud security can be a seamless extension of an organization’s network security.
One of cloud computing’s biggest security challenges is providing users with safe, frictionless access to their most essential applications. Cloud-based services are available off-premises, but the devices used to reach them are typically unprotected.
Organizations often mitigate security risks using identity and access management (IAM), a key strategy that ensures only authorized users can access specific resources. IAM solutions are not limited to cloud environments; they are integral to network security as well. These technologies include robust authentication methods, multi-factor authentication (MFA), and other access controls, all of which help protect sensitive data and systems across both on-premises and cloud-based infrastructures.
4. Endpoint security
Endpoint security focuses on protecting the devices that serve as access points to an organization’s network, such as laptops, desktops, smartphones, and tablets. These devices, or endpoints, expand the attack surface, providing potential entry points for cybercriminals to exploit vulnerabilities and infiltrate the broader infrastructure.
To reduce risk, organizations must apply the right security solutions to each endpoint, ensuring protection is tailored to the specific device and its role in the network. For example, laptops used by remote workers may require antivirus software and multi-factor authentication to prevent malware attacks or unauthorized access.
A related subset of endpoint security is mobile security, which specifically addresses the vulnerabilities of mobile devices. As employees increasingly use smartphones and tablets for work, securing these endpoints becomes critical to protecting the entire network. Security solutions, such as mobile device management, help organizations manage and secure these devices, preventing them from becoming weak links in the cybersecurity chain.
5. Application security
Application security refers to the technologies, policies, and procedures at the application level that prevent cybercriminals from exploiting application vulnerabilities. It involves a combination of mitigation strategies during application development and after deployment.
For instance, a web application firewall (WAF) monitors and filters traffic between applications and the outside world, blocking malicious activity like code injections or cross-site scripting attacks. With robust application security, organizations can ensure their software remains protected against threats that target the app and the sensitive data it processes and stores.
6. Zero trust security
Zero trust is a modern cybersecurity model that assumes no user or system, whether inside or outside the network, is automatically trustworthy by default. Instead, organizations continuously verify access to data and resources through strict authentication protocols.
Unlike traditional security models, which take a “castle-and-moat” approach, zero trust monitors more than just the perimeter. It enforces granular security controls across all endpoints, applications, and users, preventing unauthorized lateral movement. In other words, users can’t freely roam inside the network without reconfirming their identity whenever they request access to a particular resource.
7. Operational technology (OT) security
OT security, which uses the same solutions and techniques as IT environments, protects the safety and reliability of system technologies that control physical processes in a wide range of industries. This includes critical infrastructure like manufacturing systems, energy grids, and transportation networks, where a security breach could result in significant damage, but has come to include banking systems and others as well.
Traditionally, security in these environments wasn’t necessary. Most operational technologies weren’t connected to the outside world, so they didn’t require protection. Now, as IT and OT converge, they’re increasingly exposed to malicious activity.
IoT security also focuses on protecting connected devices — but on a broader scale. IoT devices range from sensors in industrial equipment to smart thermostats in homes. Because they’re web-enabled, these access points expand the attack surface. Plus, since they often have limited security capabilities, they’re vulnerable entryways for cybercriminals to exploit.
To address this, IoT security solutions focus on device authentication, encryption, and network segmentation, ensuring secure communication and preventing unauthorized access. Organizations must monitor these devices closely and implement strong access controls to minimize risks.
The inclusion of IoT security into the traditional industrial world of OT has introduced a new concept: cyber-physical systems and their security.
Cybersecurity training & certification
Cybersecurity awareness & skills development
Because people are the most vulnerable part of the cybersecurity equation, organizations must take measures to mitigate their human factors. The best way to achieve this is through end-user education — teaching the people who use technology to defend computer systems, networks, and the information therein.
At a minimum, cybersecurity awareness training ensures users can recognize and respond to common threats, like phishing, malware, and social engineering. Comprehensive cybersecurity training programs for employees go beyond basic password hygiene, covering specific risks relevant to the organization’s industry.
Many companies are turning to online platforms to make education more accessible, offering flexible cybersecurity training courses that can be completed remotely. For those seeking to deepen their expertise, cybersecurity training certification programs offer more advanced skills and recognition of their knowledge, helping employees stay current with evolving threats and security practices.
All of these efforts are to change what traditionally has been the weakest link in the chain — the human element — into an effective front line of defense and early warning system.
Cybersecurity certification programs
Cybersecurity certifications provide a structured way for professionals, regardless of experience level. Most importantly, investing in certification programs helps organizations close internal skill gaps, reduce the risk of breaches, and future-proof their cybersecurity workforce.
In fact, organizations are recognizing the significance of certified talent. According to Fortinet’s 2024 Global Skills Gap Report:
- 91% of organizations prefer hiring candidates with certifications.
- 90% of business leaders are willing to fund employee certification training.
- 95% of those with certified teams report a positive impact on performance.
Managed cybersecurity services
Managing cybersecurity can be complex and resource-intensive for many organizations. However, businesses have several options for addressing these challenges. They can choose to handle cybersecurity in-house, partner with a trusted managed security service provider (MSSP) to monitor and manage their security infrastructure, or adopt a hybrid approach that combines both internal resources and external expertise. Each option offers different benefits depending on the organization’s needs and resources, allowing them to tailor their security strategy effectively.
MSSPs offer scalable solutions that provide organizations with access to advanced cybersecurity technology, threat intelligence, and expertise without requiring them to build and maintain their own infrastructure. For example, managed services can range from basic services such as a managed firewall to more sophisticated services such as:
- MDR: Managed detection and response is a service that integrates a team of Security Operations Center (SOC) experts into your workforce. MDR provides these skilled professionals to continuously monitor user behavior and act when a threat is detected, focusing primarily on endpoint protection.
- XDR: Extended detection and response goes beyond MDR, taking a software-based approach to secure all layers — not just endpoints. It integrates MDR procedures across multiple environments to reduce the mean time to detect and protect the entire attack surface.
Types of Hackers
A Hacker is a person who is intensely interested in the mysterious workings of any computer operating system. Hackers are most often programmers. They gather advanced knowledge of operating systems and programming languages and discover loopholes within systems and the reasons for such loopholes. In this article, we will learn about all types of hackers, the Difference between White, black and, grey hat hackers, ways to protect against them.
What are The Three Main Types of Hackers?
White Hat Hackers
White hat hackers are the one who is authorized or certified hackers who work for the government and organizations by performing penetration testing and identifying loopholes in their cybersecurity. They also ensure the protection from the malicious cyber crimes. They work under the rules and regulations provided by the government, that’s why they are called Ethical hackers or Cybersecurity experts.
Black Hat Hackers
They are often called Crackers. Black Hat Hackers can gain unauthorized access to your system and destroy your vital data. The method of attack they use common hacking practices they have learned earlier. They are considered to be criminals and can be easily identified because of their malicious actions.
Gray Hat Hackers
Gray hat hackers fall somewhere in the category between white hat and black hat hackers. They are not legally authorized hackers. They work with both good and bad intentions, they can use their skills for personal gain. It all depends upon the hacker. If a gray hat hacker uses his skill for his personal gains, he/she is considered as black hat hackers.

Other Types of Hackers
There are generally 7 types of Hackers, after the main 3 types, they are:
- Script Kiddies: They are the most dangerous people in terms of hackers. A Script kiddie is an unskilled person who uses scripts or downloads tools available for hacking provided by other hackers. They attempt to attack computer systems and networks and deface websites. Their main purpose is to impress their friends and society. Generally, Script Kiddies are juveniles who are unskilled about hacking.
- Green Hat Hackers: They are also amateurs in the world of hacking but they are bit different from script kiddies. They care about hacking and strive to become full-blown hackers. They are inspired by the hackers and ask them few questions about. While hackers are answering their question they will listen to its novelty.
- Blue Hat Hackers: They are much like the white hat hackers, they work for companies for security testing of their software right before the product launch. Blue hat hackers are outsourced by the company unlike white hat hackers which are employed by the (part of the) company.
- Red Hat Hackers: They are also known as the eagle-eyed hackers. Like white hat hackers, red hat hackers also aims to halt the black hat hackers. There is a major difference in the way they operate. They become ruthless while dealing with malware actions of the black hat hackers. Red hat hacker will keep on attacking the hacker aggressively that the hacker may know it as well have to replace the whole system.
- State/Nation Sponsored Hackers: State or Nation sponsored hackers are those who are appointed by the government to provide them cybersecurity and to gain confidential information from other countries to stay at the top or to avoid any kind of danger to the country. They are highly paid government workers.
- Hacktivist: These are also called the online versions of the activists. Hacktivist is a hacker or a group of anonymous hackers who gain unauthorized access to government’s computer files and networks for further social or political ends.
- Malicious Insider or Whistleblower: A malicious insider or a whistleblower could be an employee of a company or a government agency with a grudge or a strategic employee who becomes aware of any illegal activities happening within the organization and can blackmail the organization for his/her personal gain.
What’s the Difference Between White, Black, and Gray Hat Hackers?
White hat hackers are ethical hackers who help improve cybersecurity by identifying and fixing vulnerabilities in systems. They work with organizations to enhance security measures and protect sensitive data. Black hat hackers, on the other hand, engage in malicious activities for personal gain, exploiting system weaknesses to steal, alter, or destroy data. Gray hat hackers fall somewhere in between, as they may break laws or ethical guidelines but do not have malicious intent. Understanding the differences between white, black, and gray hat hackers is essential for grasping the diverse landscape of hacking and the various motivations behind these activities. By recognizing these distinctions, organizations can better address security challenges and foster a safer digital environment.
Ways to Protect Against Hackers
Protecting against hackers involves implementing various cybersecurity measures to safeguard your data and systems.
- Regularly updating software and operating systems ensures that security patches are applied to fix vulnerabilities.
- Using strong, unique passwords for different accounts and enabling two-factor authentication adds an extra layer of security.
- Installing and maintaining reliable antivirus software helps detect and remove malware.
- Educating employees and users about phishing and social engineering tactics can prevent successful attacks.
- Additionally, securing networks with firewalls and encryption protects sensitive information from unauthorized access.
By adopting these practices, individuals and organizations can significantly reduce the risk of hacking and enhance their overall cybersecurity posture.
Conclusion
Understanding the different types of hackers is essential for developing effective cybersecurity strategies. White hat hackers play a crucial role in enhancing security by identifying and fixing vulnerabilities, while black hat hackers pose significant threats through malicious activities. Gray hat hackers, operating in the middle ground, highlight the complexities of hacking motivations.
