PortFast STP PortFast is a feature in Cisco switches that makes an access port go to Forwarding state immediately, instead of waiting through normal STP states. This helps end devices connect faster.
Normal STP Port Process?
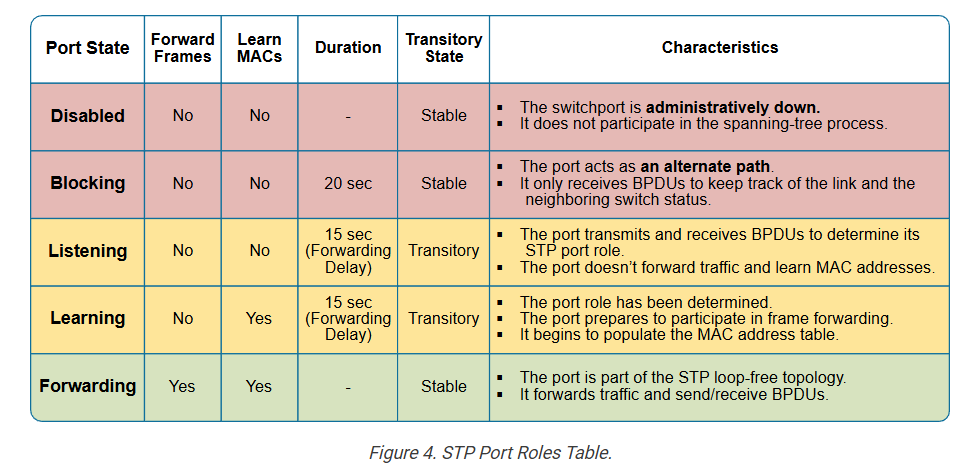
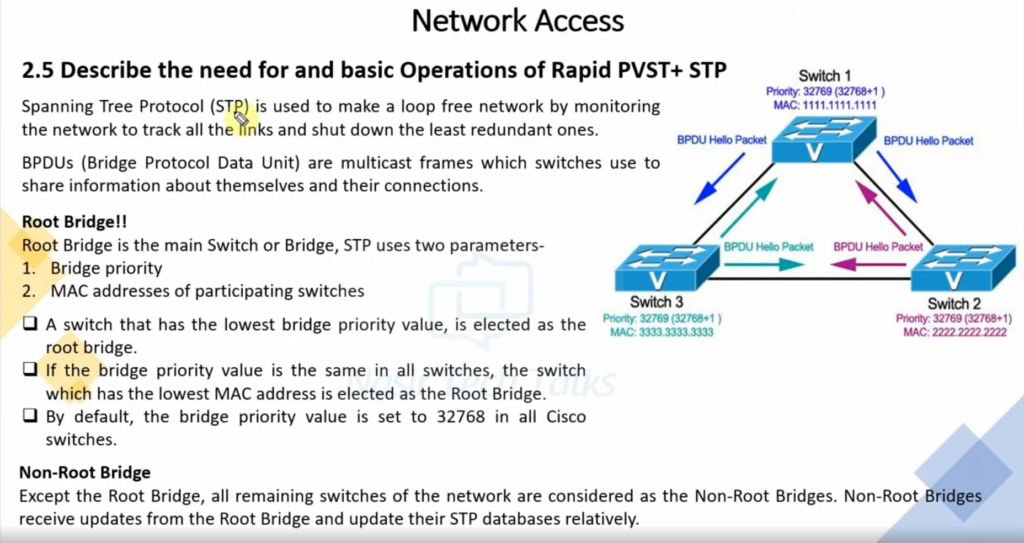
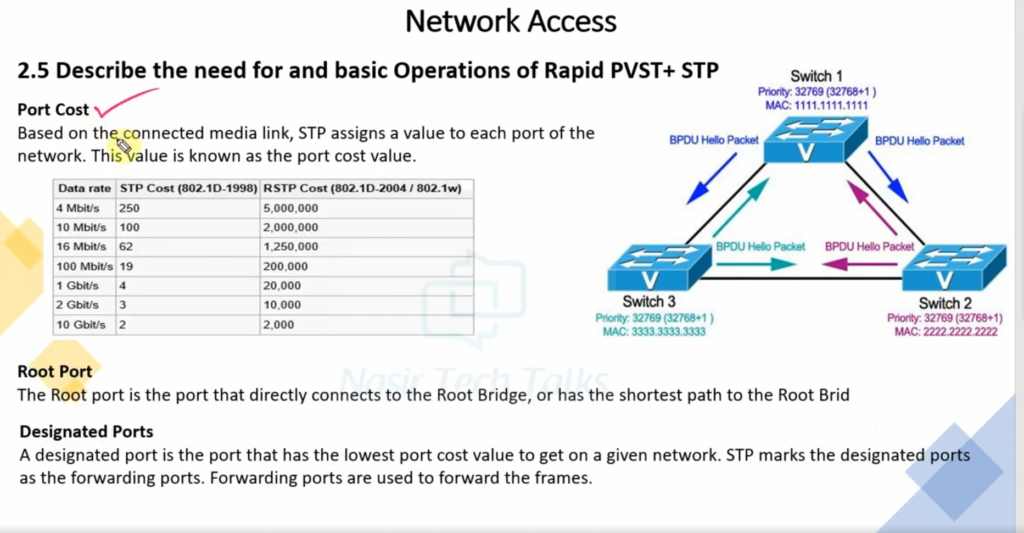
In normal Spanning Tree Protocol STP, when a port comes up, it passes through Blocking → Listening → Learning → Forwarding. This process can take around 30–50 seconds before data starts flowing. During this time, devices may not get network access immediately.
How PortFast Works?
With PortFast enabled, the switch port skips Listening and Learning delay and directly enters Forwarding state. As soon as a PC, printer, IP phone, or server connects, network communication starts quickly.
Example:
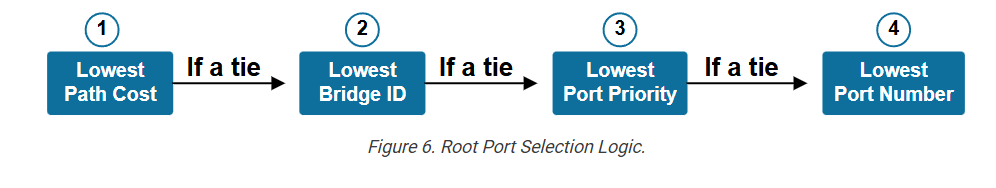
Suppose a computer is connected to a switch port. Without PortFast, the computer may wait several seconds before getting network access or an IP address. With PortFast enabled, the port forwards traffic immediately, so the computer connects faster.
Where to Use?
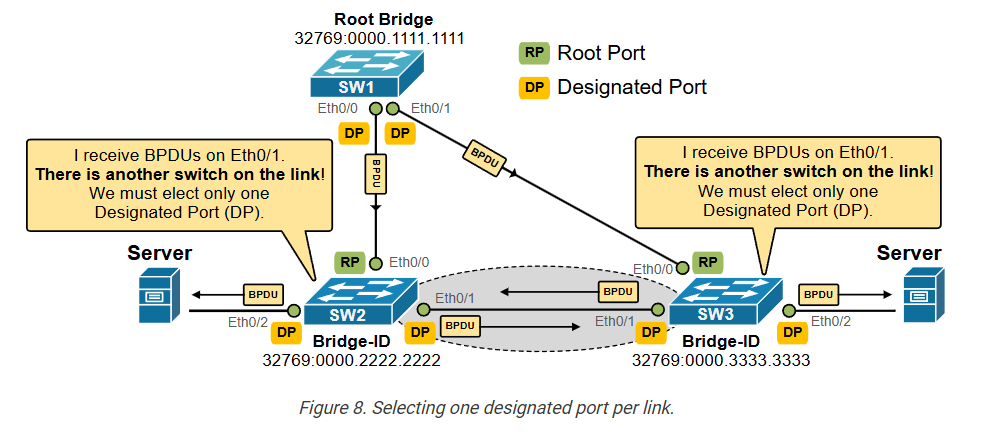
PortFast should be enabled on access ports connected to end devices like PCs, printers, IP phones, and servers. It should not be enabled on switch-to-switch links, because that can create network loops.
Benefit?
PortFast provides fast connectivity, reduces waiting time for devices, and helps services like DHCP start quickly after a device connects.
spanning-tree feature called PortFast. It is used to optimize the ports that connect to end-user devices by skipping the Listening and Learning state and directly putting the ports to Forwarding.
Why do we need STP Portfast?
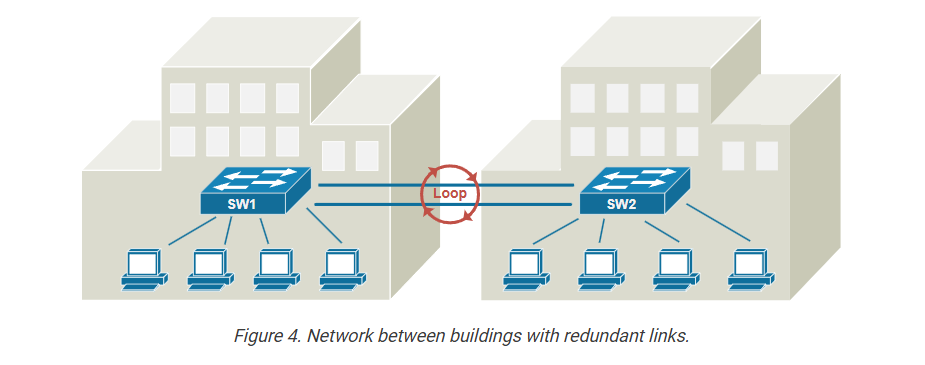
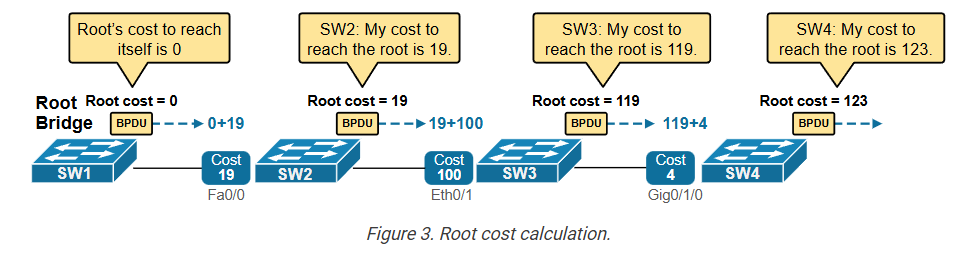
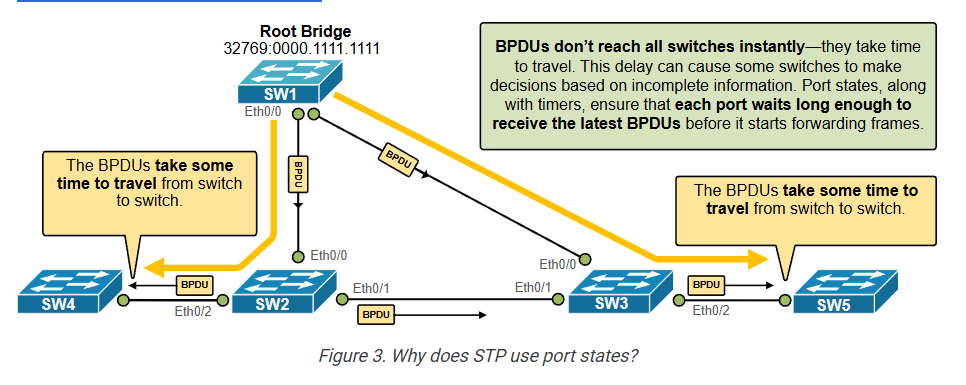
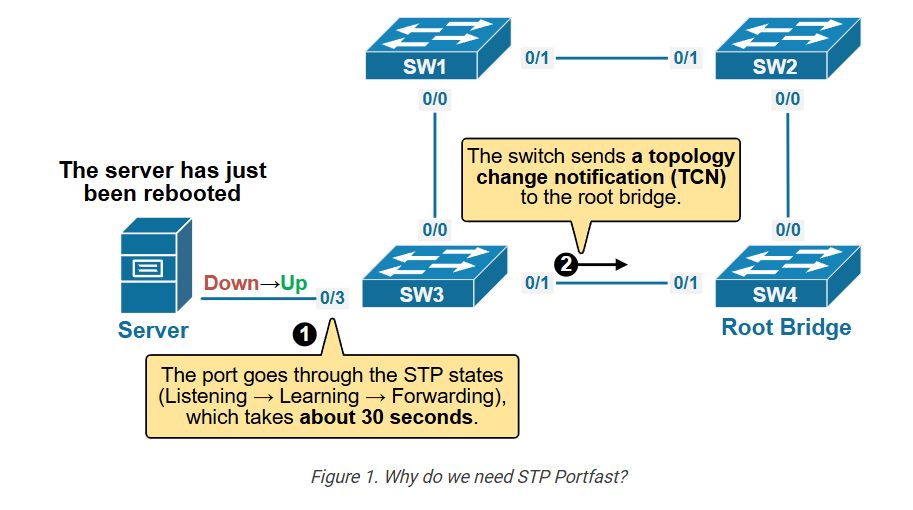
To understand why the Spanning Tree protocol has introduced the Portfast feature, let’s examine the following example. Imagine a server connected to a switch port that is not configured with PortFast. When the server reboots, the switchport goes down and then comes back up. This triggers Spanning Tree to do the following:
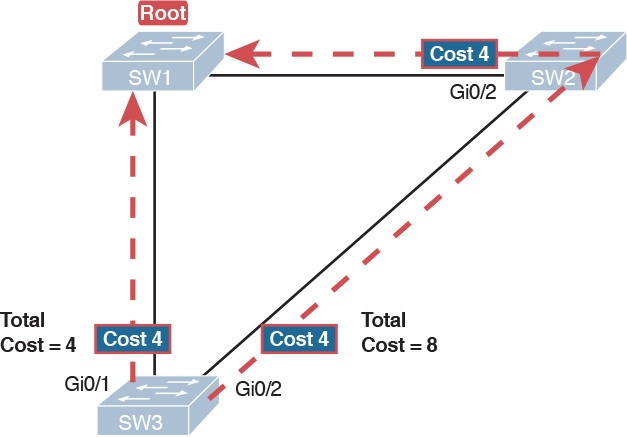
- The Spanning-Tree protocol starts its normal process of putting the interface in a forwarding state. The port transitions to the Listening state (15 seconds), then to the Learning state (15 seconds), and finally, it moves to the Forwarding state. So, the port takes about 30 seconds before the server can send and receive data.
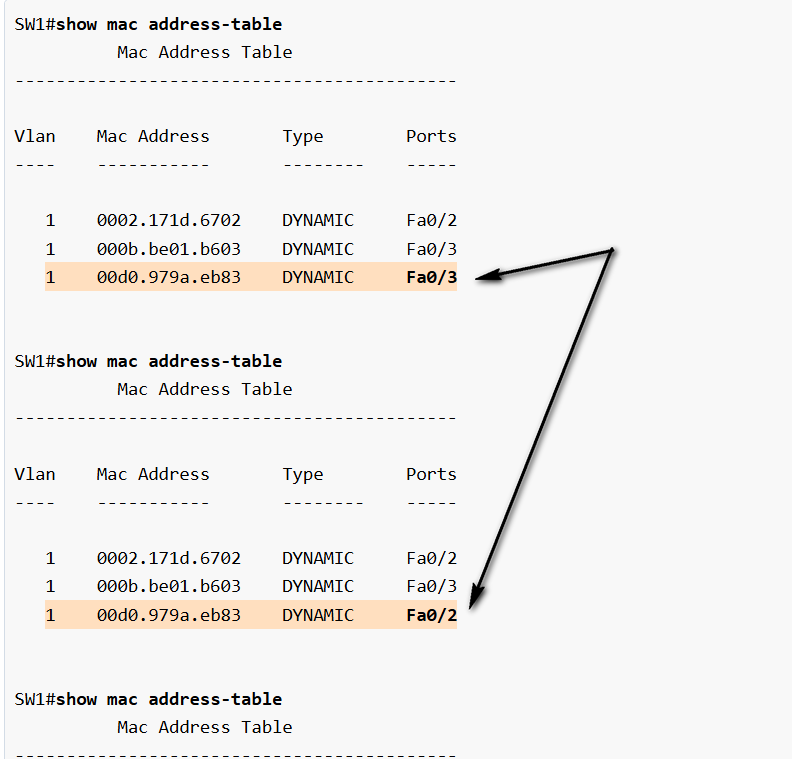
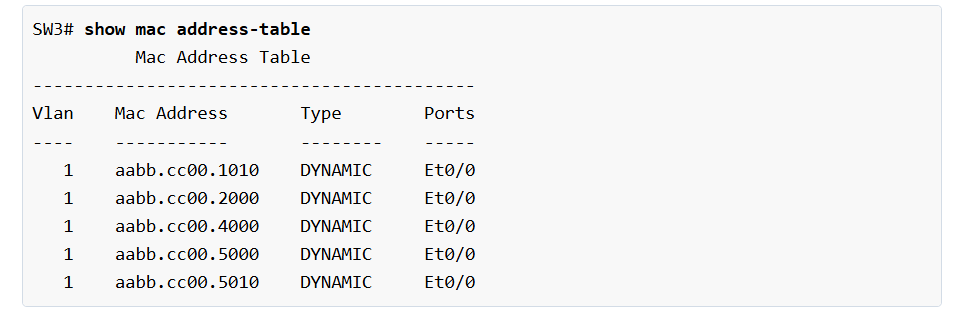
- The switch sees this link flap as a topology change and triggers the Topology Change Notification (TCN) process.. In short, when a topology change is detected, switches lower their MAC table aging timer (5 min) to the MaxAge time (20 sec).
However, if a switchport connects only to one end-user device (like a server, computer, printer, etc.), there’s very little risk of a loop. Loops only occur when the device is bridging traffic back into the network, which end-user devices do not do.
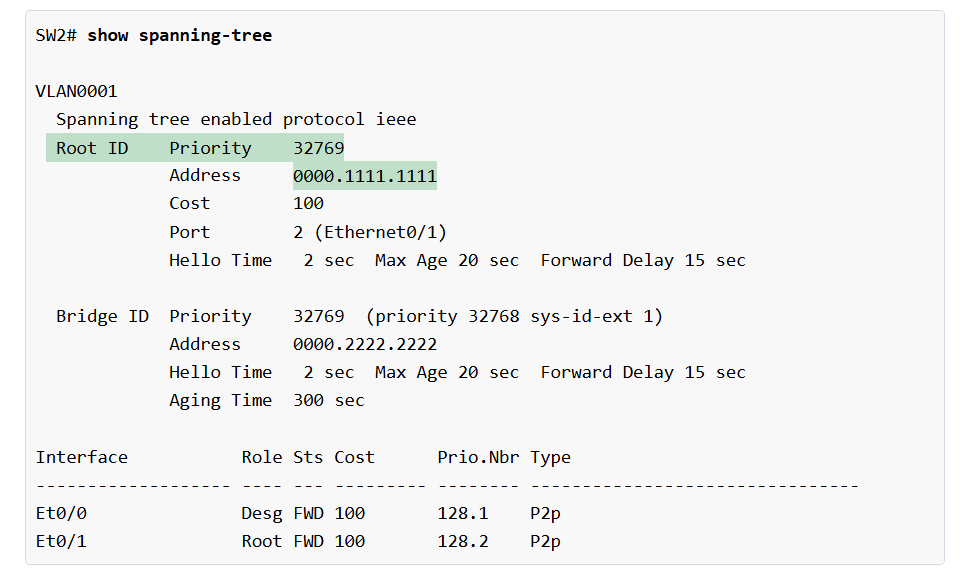
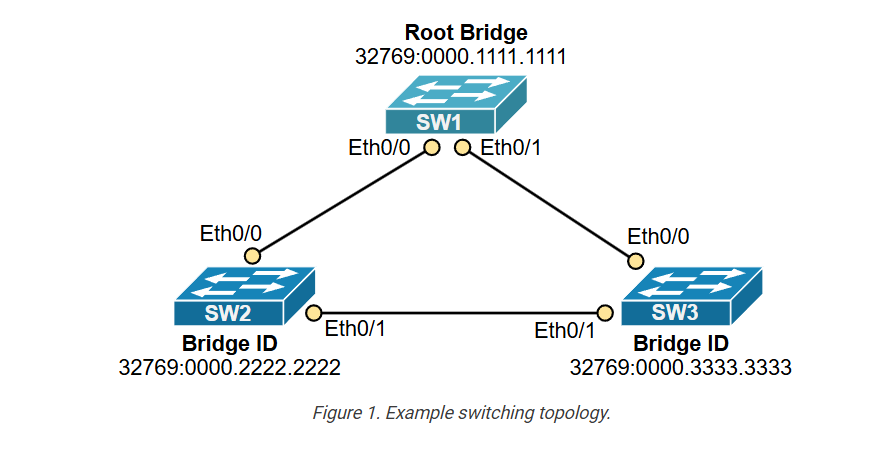
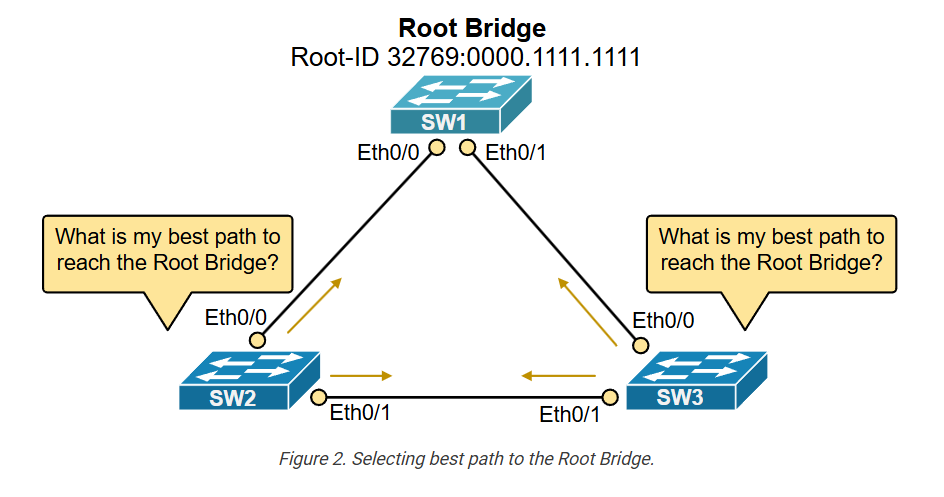
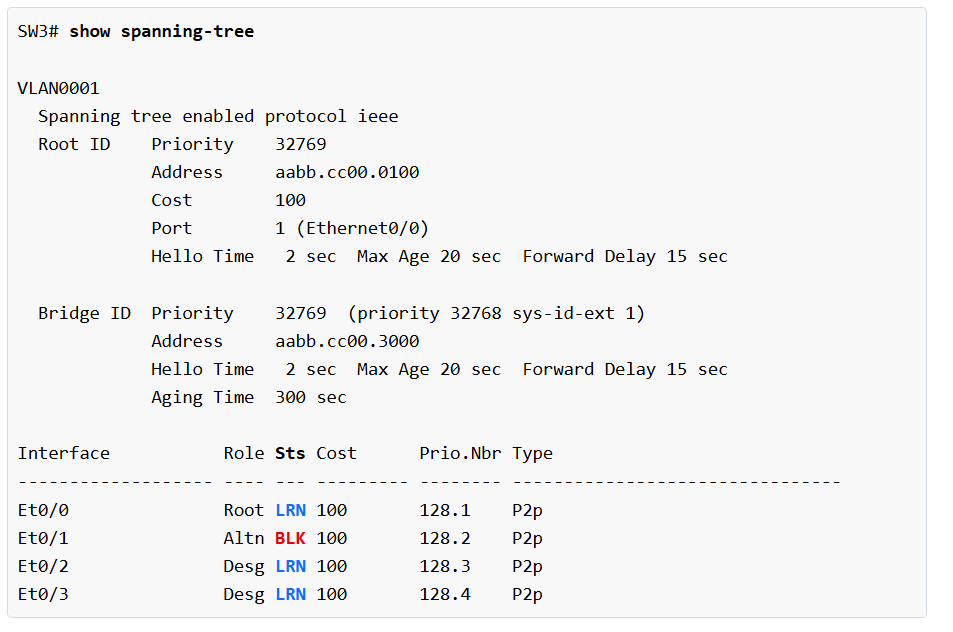
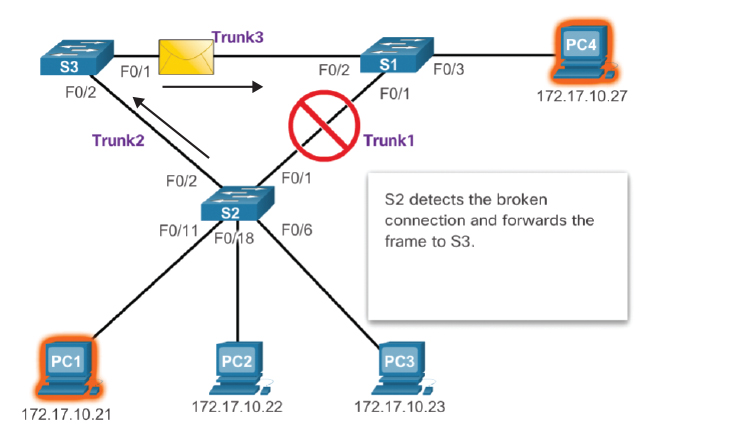
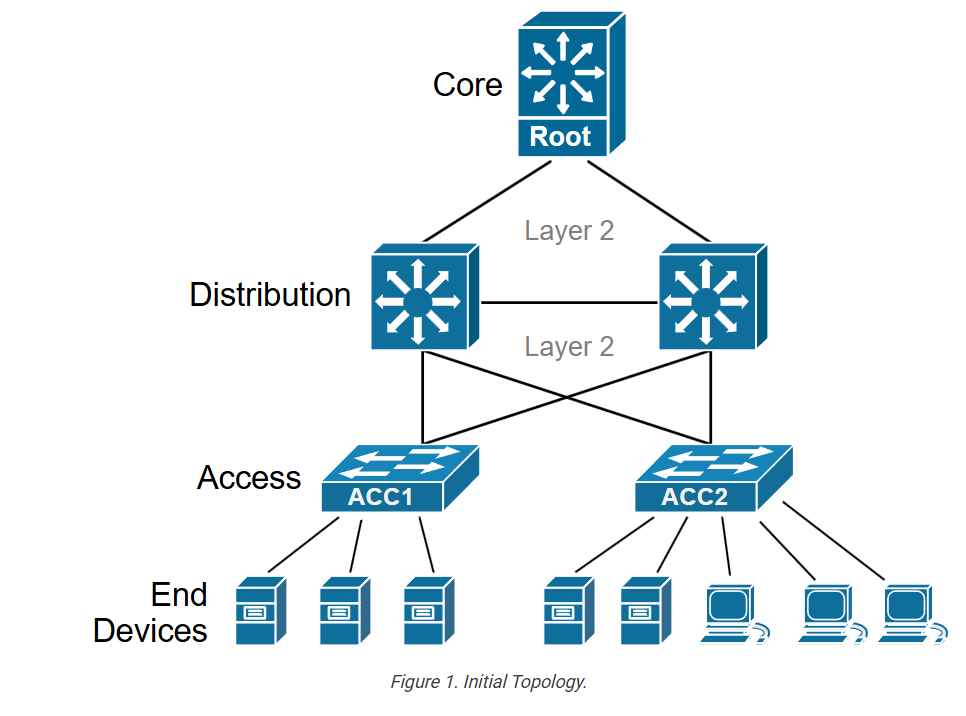
Let’s use the topology shown in the diagram below to demonstrate this STP behavior. We will power up the server and observe how STP reacts.
The server connects to port Eth0/3, which is a standard port that is not configured with the PortFast feature. To simulate the server powering up, we enable the interface, as shown in the output below. Notice that we turned the debug spanning-tree events command on to see what happens.
Notice the times in the debug outputs. It took STP 30 seconds to put the port in the forwarding state. Nowadays, servers boot much faster than that. Additionally, servers attempt to assign IPv4/IPv6/DNS settings via DHCP during their boot-up process. Therefore, servers need to access the network immediately after they are powered on, and the spanning tree protocol becomes a bottleneck.
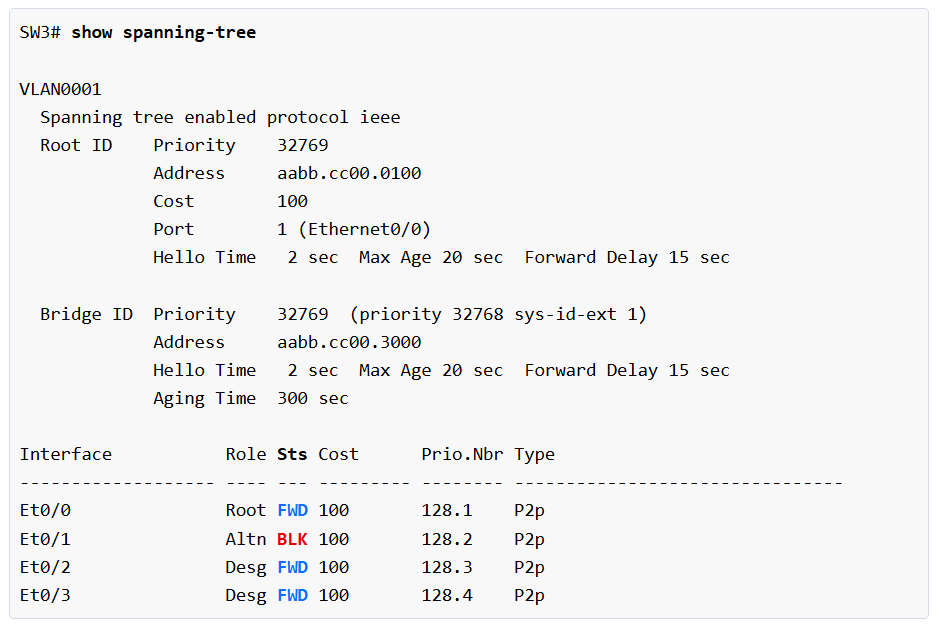
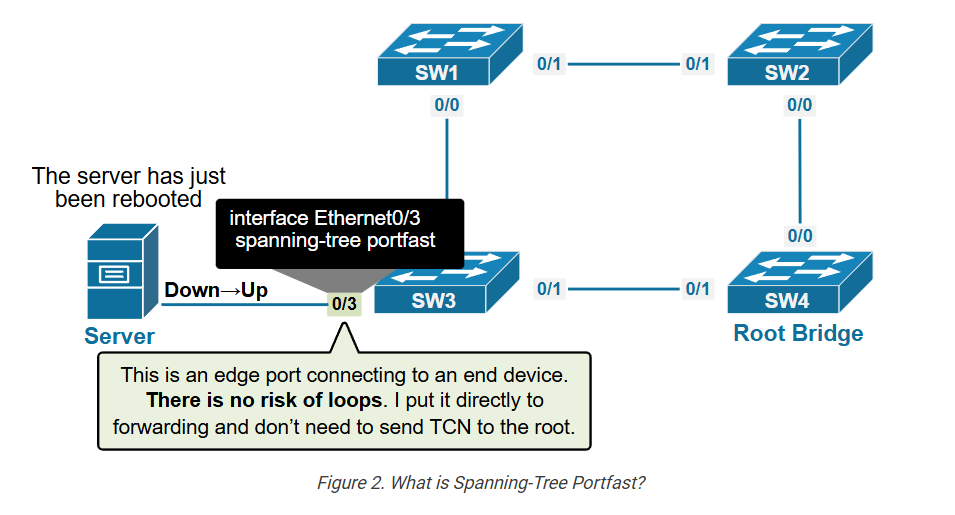
To fix this 30-second delay, the STP protocol has introduced the PortFast feature, which skips the Listening and Learning states and moves the port straight to Forwarding.
What is Portfast?
PortFast is a spanning-tree feature that optimizes the handling of edge ports. Edge ports are ones that connect to end-user devices such as computers, servers, and printers. PortFast is configured per port and provides two significant optimizations when enabled:
- When the port becomes up, STP puts it into a Forwarding state right away, skipping the Listening and Learning states.
- When the port status changes, STP does not generate a Topology Change Notifications (TCNs).
Note: In the context of Spanning-Tree, an edge port is a switch port that is directly connected to an end-user device, such as a computer, printer, or server.
Portfast must be used only on edge ports. It should not be used on ports connected to other switches or hubs, as this can cause temporary loops.
How does Portfast work?
PortFast was introduced to solve a problem where an end-user device couldn’t get a DHCP address because the switch port took 30 seconds to go through the STP states and start forwarding traffic. PortFast skips the Listening and Learning steps and puts the port directly into the Forwarding state so that the end device can immediately access the network.
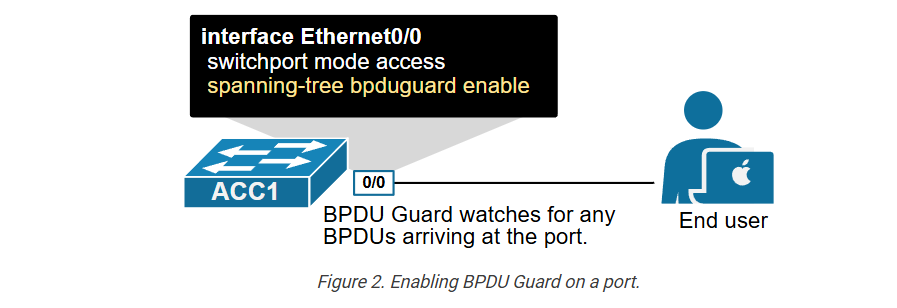
The feature works per interface. There are two ways to enable it: globally on all interfaces at once or locally at one interface at a time. The following output shows how we configure the future on one interface only.
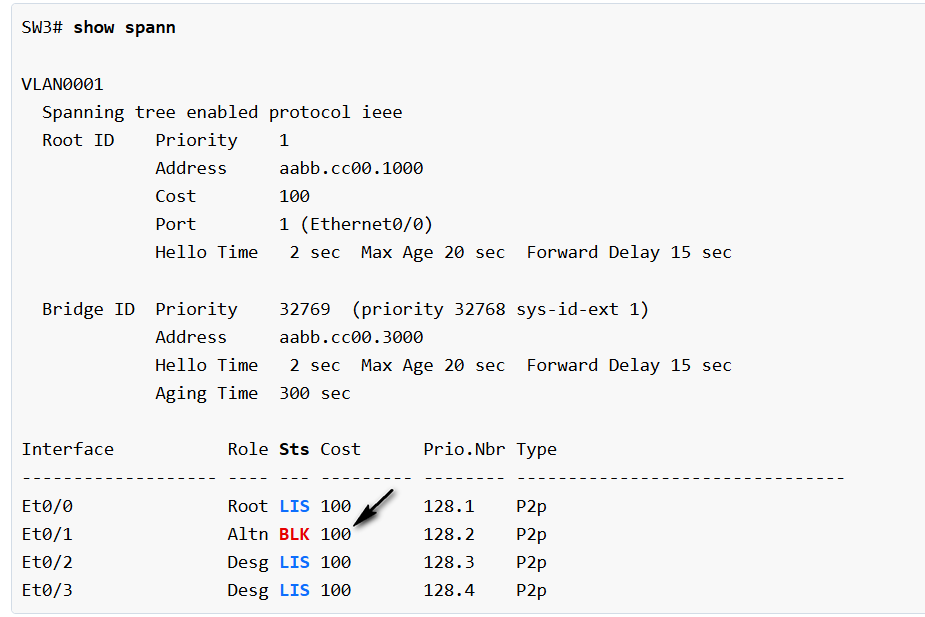
Now, if we change the port’s state, we can see that it “jumps directly from blocking to forwarding,” skipping the Listening and Learning states.
Notice that the interface is now listed as an edge port. It means that the spanning-tree protocol knows that this interface connects to an end-user device.
We can verify that the interface is configured with Portfast using the following show command.
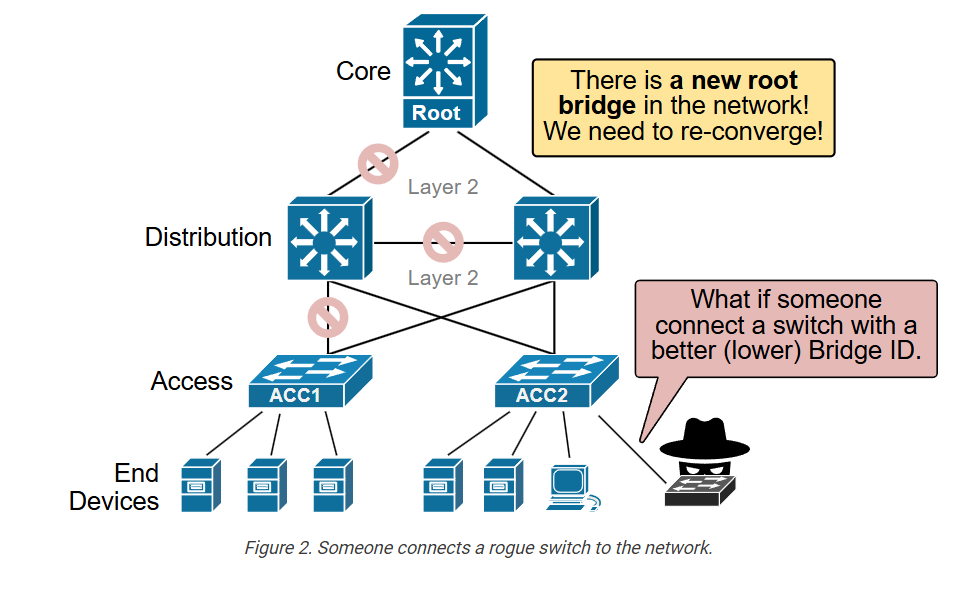
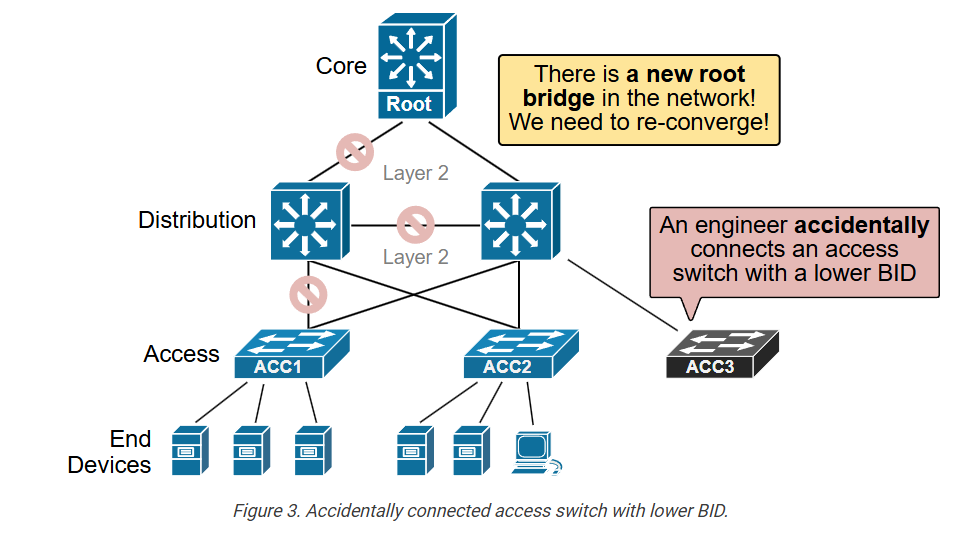
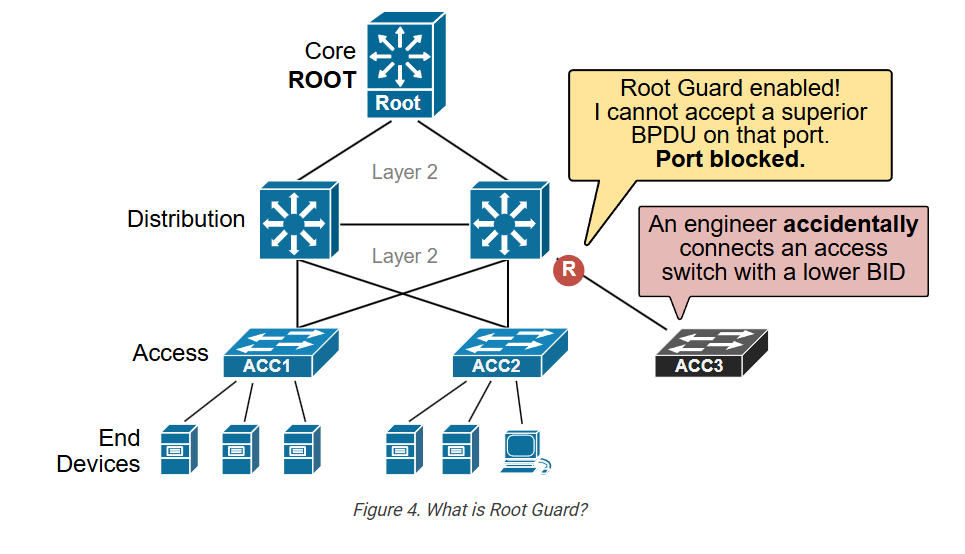
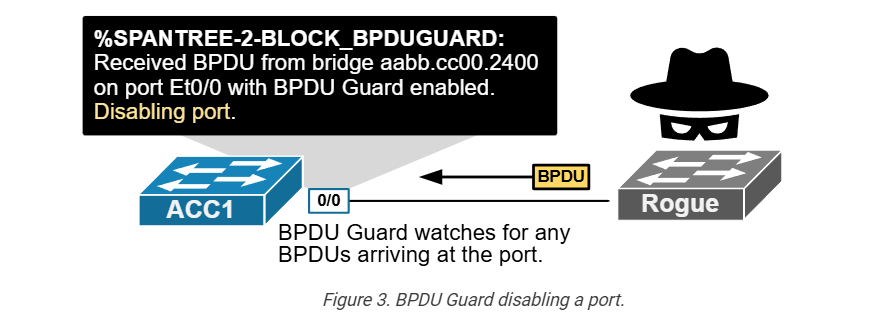
Connecting a switch to an edge port
Since we have repeatedly stated that the feature should only be used on ports that connect to end-user devices, some people might wonder:
“Okay, but what will happen if someone accidentally connects a switch to a Portfast interface?”
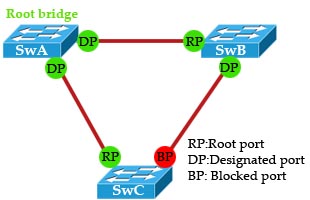
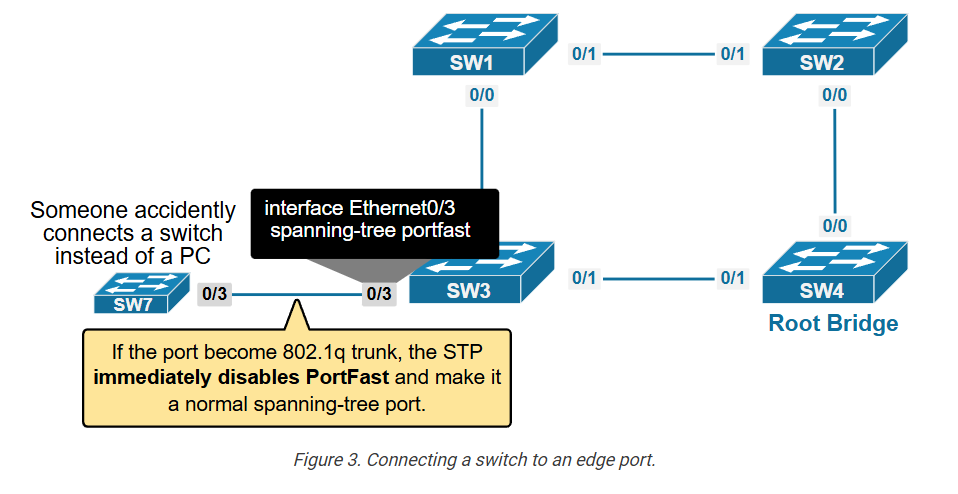
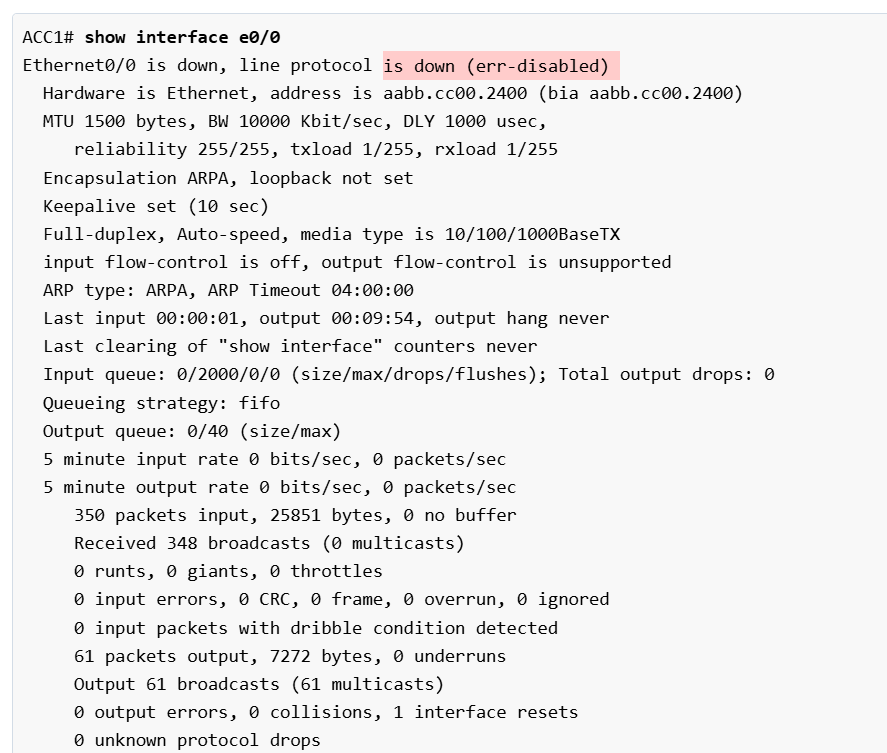
It’s essential to understand the distinction between PortFast’s administrative and operational states. The administrative state is what you’ve configured, while the operational state shows whether the feature is actually active on a given port. Let’s see what happens when we connect a switch to the interface Eth0/3, as shown in the diagram below.
As soon as we connect a switch to interface Eth0/3, the port goes into the Listening and Learning states, as shown in the output below.
Essentially, the spanning-tree protocol reverts the port to a normal state to prevent potential loops. It also sends a topology change notification to the root bridge to inform it that the switch topology has changed (a new switch is added to the topology).
Now, if we check the interface’s operational state, we can see that the feature is operationally disabled, even though the port is configured with Portfast. Also, notice that the interface is no longer considered an edge port by the spanning tree.
PortFast should only be used on ports that connect to end devices, like servers, PCs, or printers. Therefore, the switch only turns on the feature on access ports and automatically disables it on trunk ports, which connect to other switches.
Note: Portfast only works on access ports. If an interface becomes an 802.1Q trunk, the feature is automatically disabled.
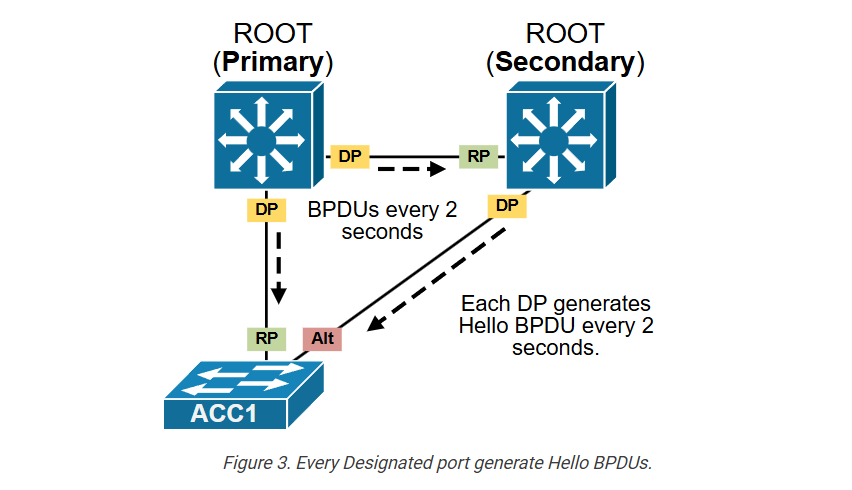
Portfast and BPDUs
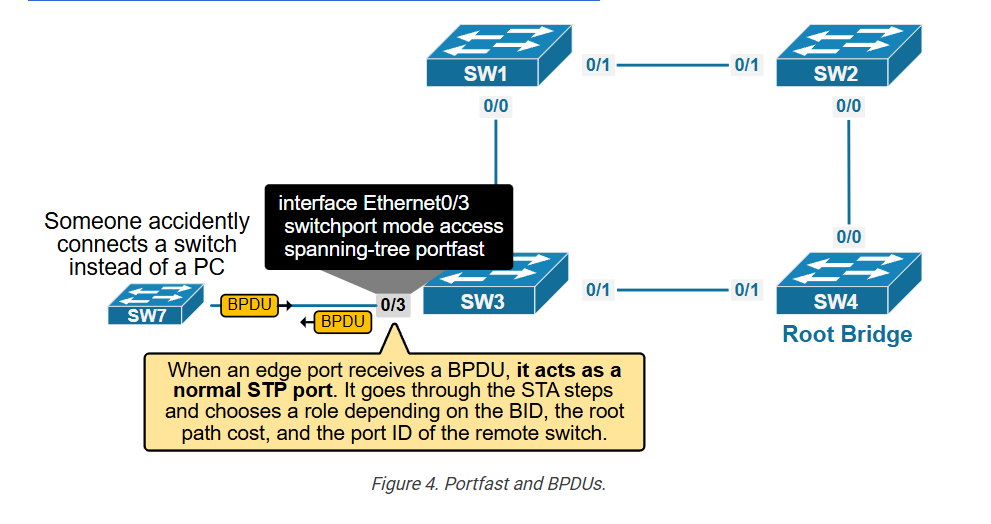
There’s a lot of confusion online about how the feature works in the context of BPDUs. A common misunderstanding is that it disables STP and stops sending or receiving BPDUs. That’s not true. A PortFast-enabled port still sends and receives BPDUs as every designated STP port does. In fact, if a PortFast port receives a BPDU, it acts as a normal STP port. It goes through the Spanning-Tree Algorithm (STA) steps and chooses a role (Root, Desg, or Altn) depending on the BID, the root path cost, and the port ID of the remote switch.
In our example, SW7 is a stub switch—it doesn’t have any other inter-switch connections. Additionally, the link between the switches is not an 802.1q trunk. In that case, SW3’s eth0/3 interface becomes a designated port and still works in a Portfast mode, as shown in the output below, even though it received a few BPDUs from SW7.
Notice two important points here:
- SW3’s interface Eth0/3 still sends and receives BPDUs even though it is configured with Portfast.
- It acts as a normal STP port when processing remote BPDUs. If the remote switch sends superior BPDUs, the port can go into a blocking state to prevent loops.
Now, let’s shift our focus to the different methods for enabling the feature on switchports.
Configuring Portfast on Edge ports:
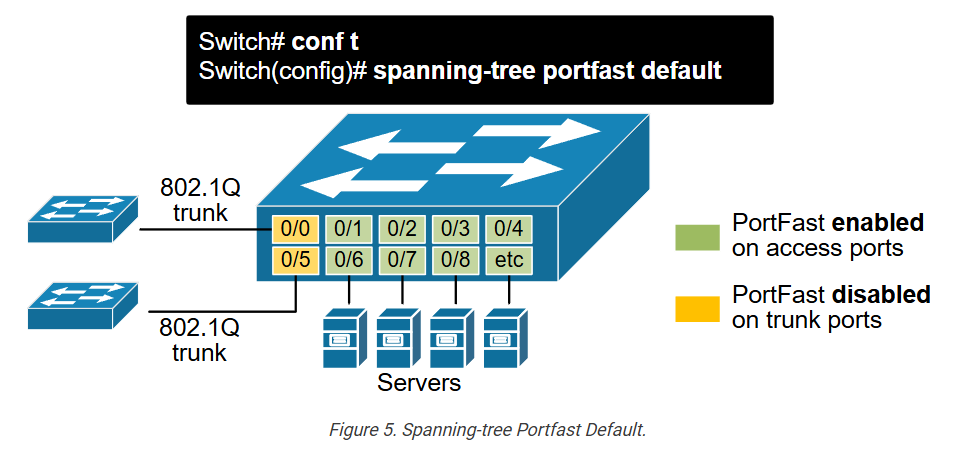
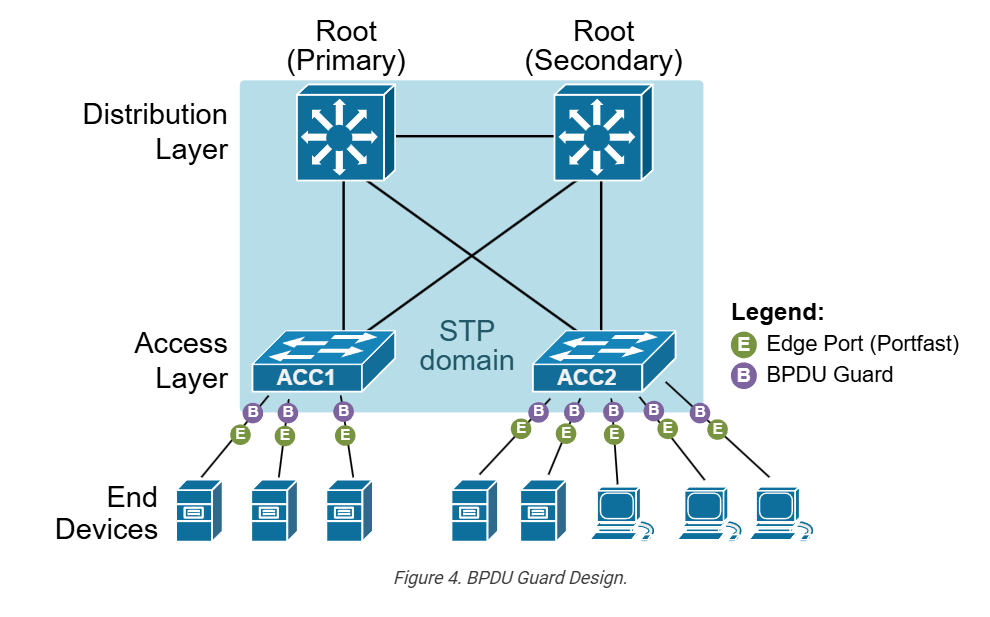
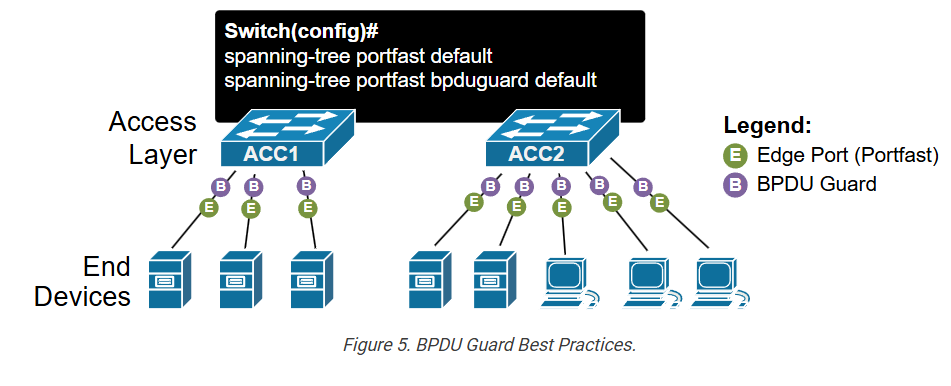
The Portfast feature is disabled by default on all switchports. There are two methods you can use to configure it on one or many ports. You can enable it globally using the spanning-tree portfast default or per interface using spanning-tree portfast. In both cases, it only works on access ports.
Option 1: Enable Portfast globally:
You can set PortFast as the default for all switch ports with one global command, as shown in the diagram below.
This will automatically enable the feature on all ports that are in access mode (non-trunking) and will disable the feature on the ones that are 802.1Q trunks.
We can verify if the command is configured on the switch using the following command.
Note that this is now the recommended approach in all modern networks and is included in all validated design guides. If a switchport connects to a single device, such as a server, printer, or PC, there is absolutely no reason not to enable the Portfast feature.
Option 2: Enable Portfast per-interface?
The other, more granular way to enable the feature is to use the interface-level command, as shown in the output below.
This approach is useful in scenarios when you want to enable the feature only on specific interfaces.
Using the Switchport Host macro?
You can also use a macro command switchport host that configures the port as access and configures Portfast, as you can see in the output below.
In the output below, you can see that the macro command configured two individual commands that make the interface and edge port.
The switchport host is typically not widely used, but it can be handy in exam environments, depending on the requirements.
Portfast Design Considerations
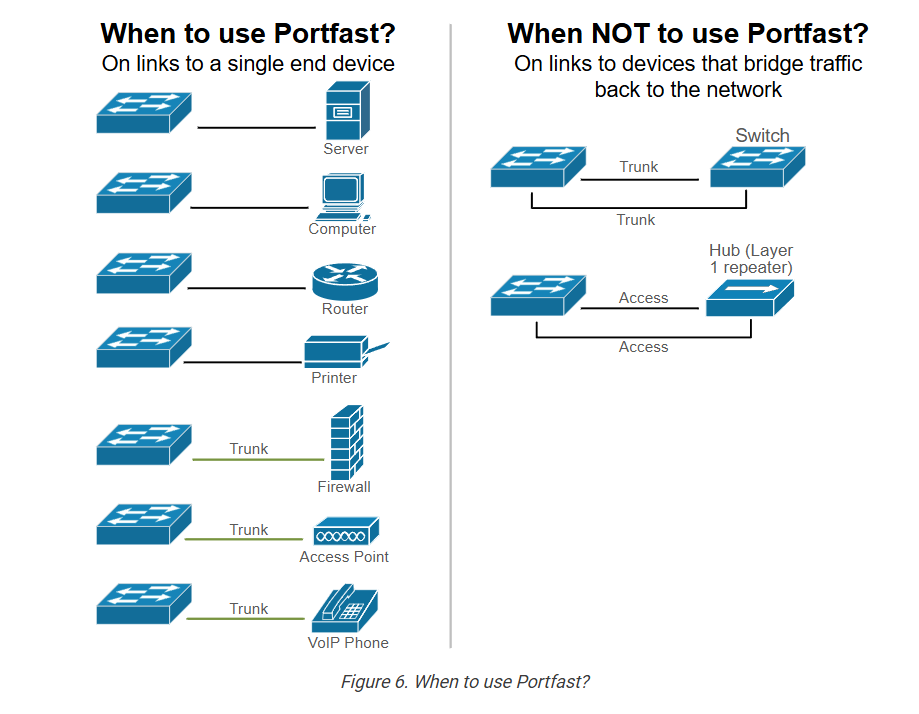
Now let’s shift our focus on the design point of view of the feature. When should you use it, and when not?
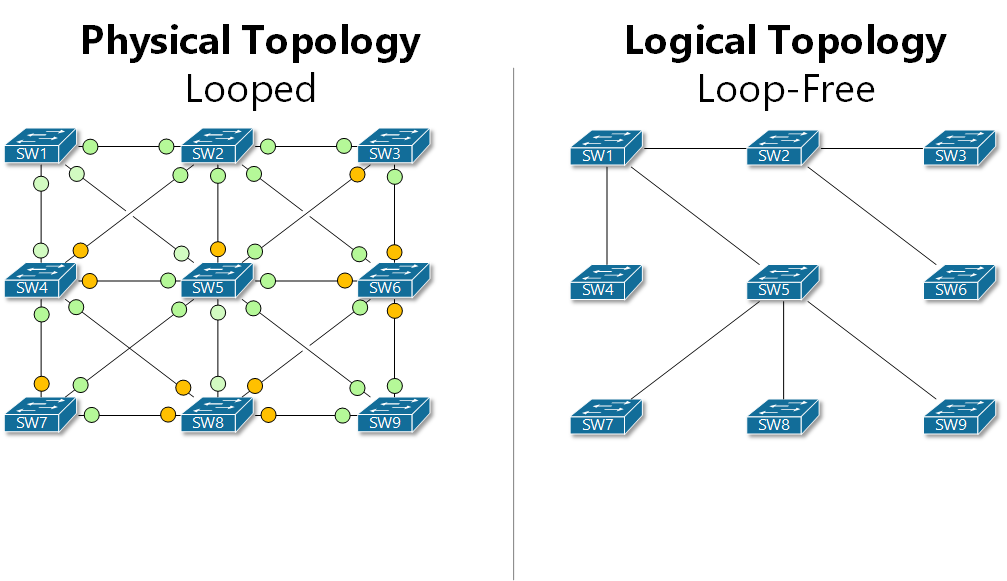
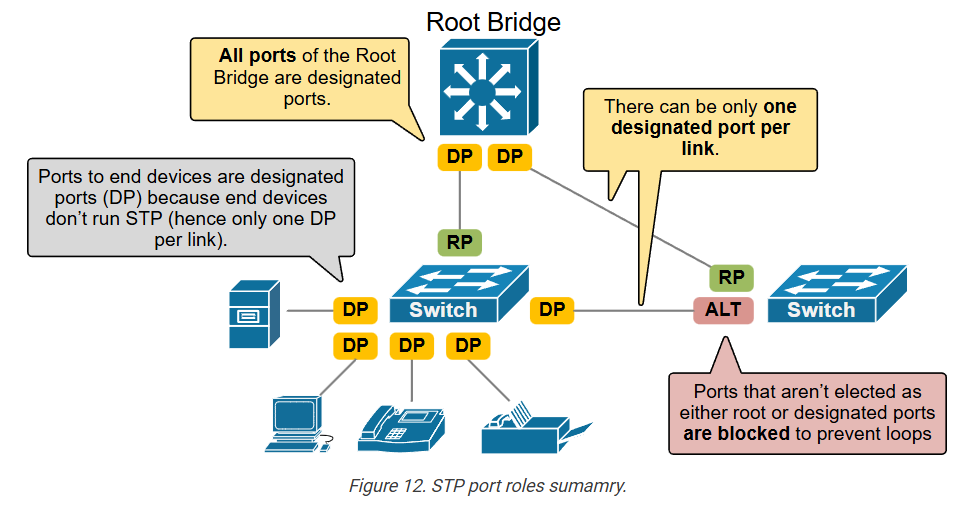
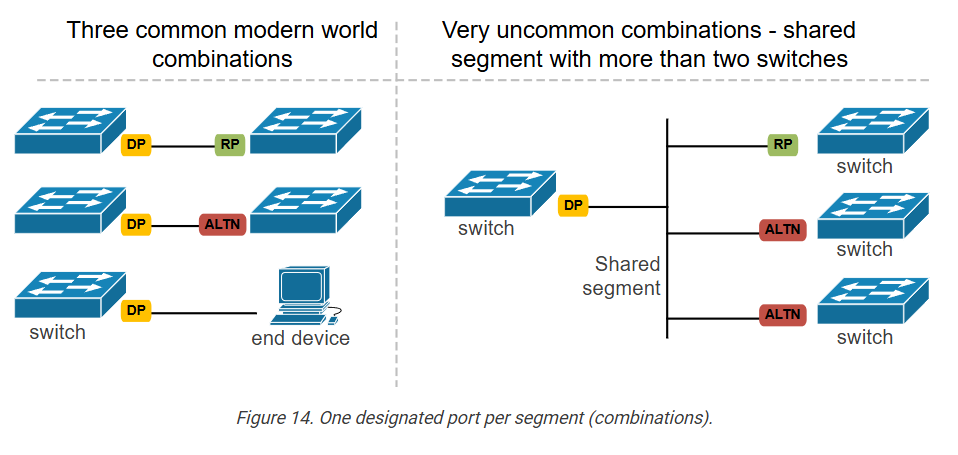
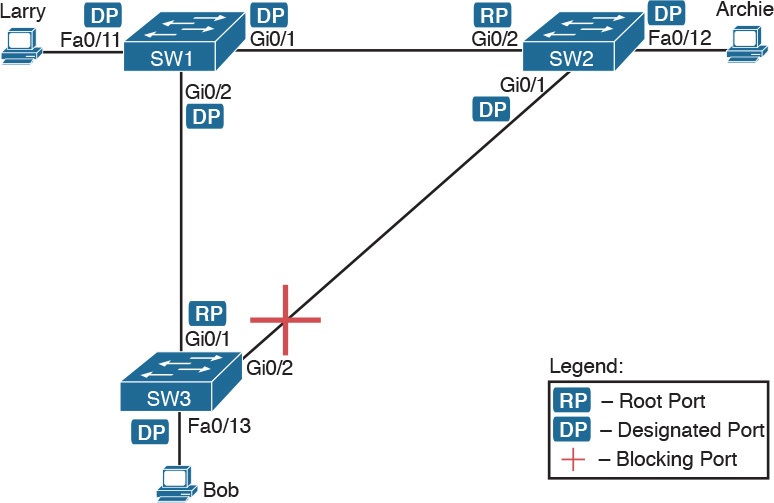
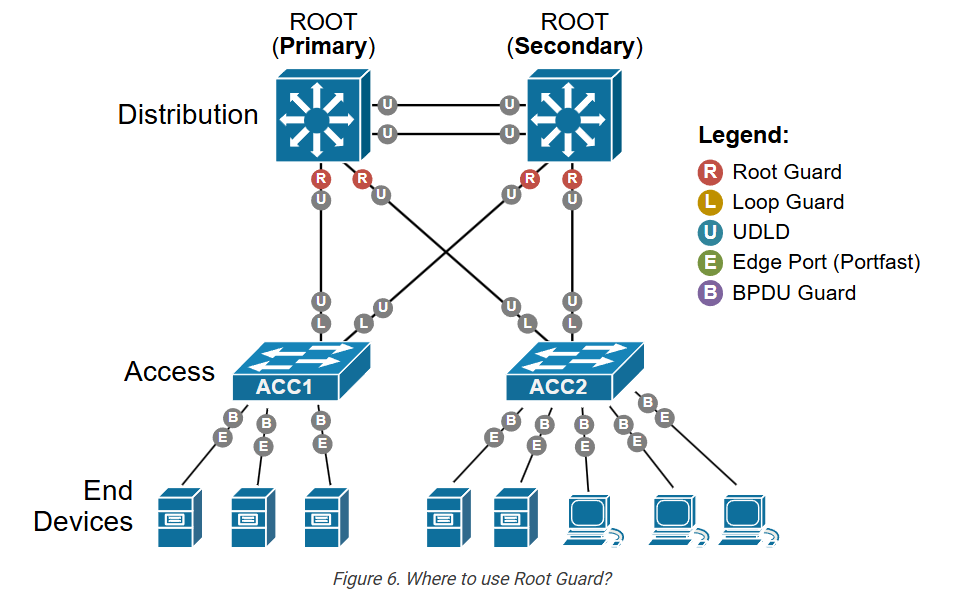
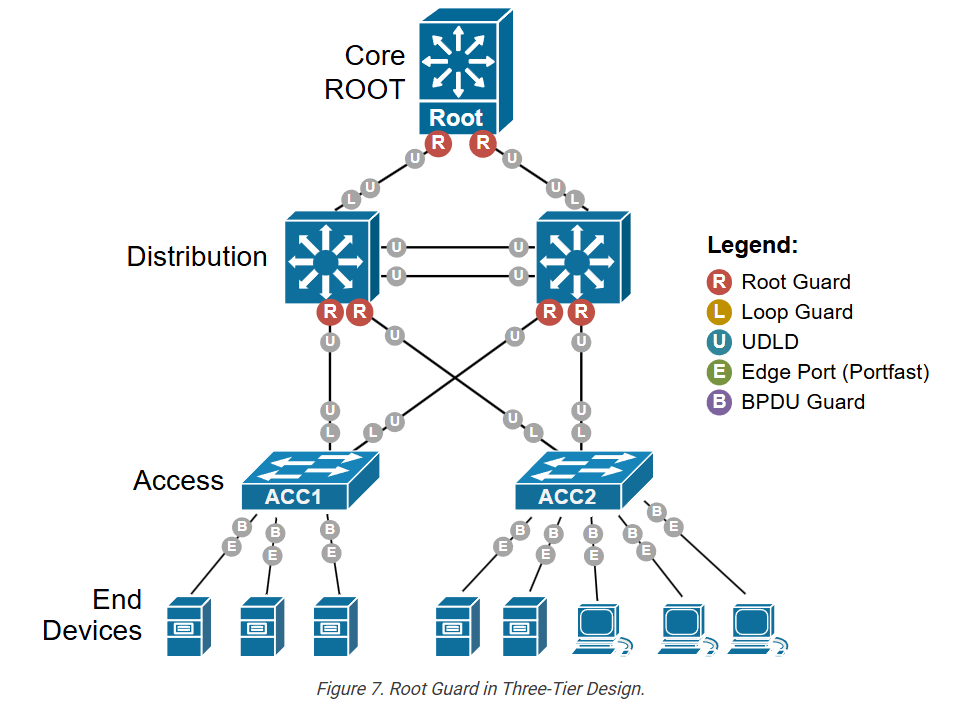
The following diagram shows the most common scenarios when it is appropriate to use the PortFast feature and when it is not.
The general rule of thumb is this: Use PortFast on all ports connected to end-user devices, like computers, printers, or phones. Do NOT use PortFast on ports connected to other switches and hubs that bridge traffic back to the network and can cause loops. The logic behind it is this:
- On end devices, there’s no risk of loops, so skipping STP saves time.
- On switch-to-switch links, skipping the Listening and Learning states can cause temporary loops and harm the network.
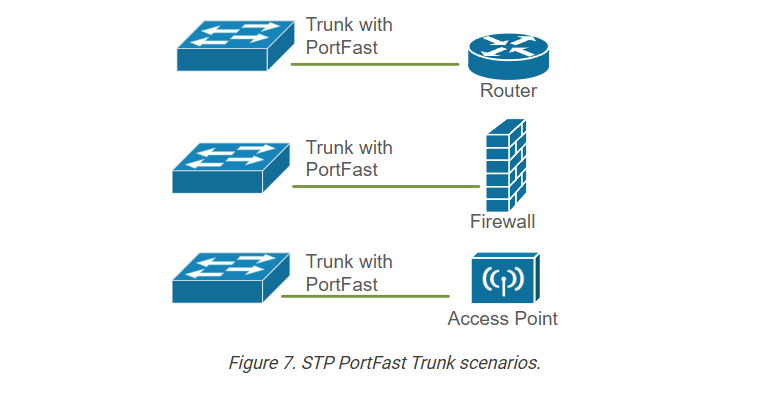
Portfast Trunks:
Notice some special cases in the diagram above. Some of the links connecting to end devices, like access points, are actually trunks. For example, an access point can have multiple SSIDs that map to different wired VLANs. Therefore, the link to the access point (AP) must be a trunk link that carries multiple VLANs. On the other hand, the AP is an end device and does not bridge traffic back to the network. It simply provides connectivity to wireless clients. In that case, it is ok to use Portfast on the port connected to the AP to save time when the link flaps. But wait, Portfast only works on access ports, right?
In some cases, as shown in the diagram above, you may want to connect a device to a trunk port to avoid STP delays. The most common examples are access points, routers, and firewalls that connect multiple VLANs on sub-interfaces. To account for these scenarios, Cisco has introduced the spanning-tree portfast trunk command, as shown below.
It makes the trunk port skip the usual Spanning Tree Protocol (STP) states (listening and learning) and go immediately to forwarding. Only use it when you know there will be no loops. Cisco recommends using it only in controlled environments because it bypasses loop protection at startup.
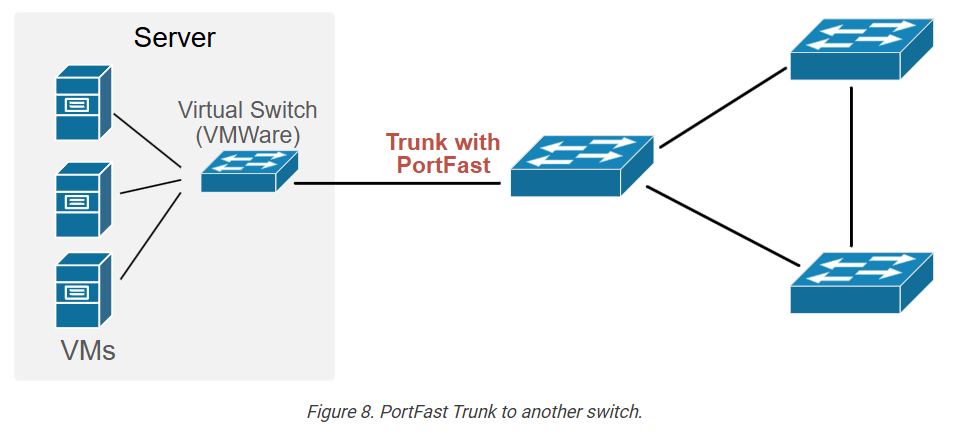
PortFast Trunk to another Switch:
In some cases, you can go even further and use the spanning-tree portfast trunk command on a link that connects another switch. One example is to connect to a VMware ESXi host that runs multiple virtual machines and a virtual switch, as shown in the diagram below.
In that case, the virtual switch is not part of the spanning tree topology. It does not bridge traffic back to the network. It is a stub switch that simply connects virtual machines to different VLANs. The risk of loops is very low. The goal is to avoid the 30-second delay caused by STP and provide fast link initialization to avoid delays during VM boot.
Key Takeaways
Now, let’s summarize what we have discussed in this lesson and highlight the essential points to take away from this lesson.
Why do we need Portfast in modern networks?
- When a server connects to a regular STP port, it might not get an IP address through DHCP because the port takes about 30 seconds to enter the Forwarding state (15-sec Listening and 15-sec Learning equal 30 seconds).
- Additionally, when a regular STP port changes its physical state (goes down and up again), the switch sends a Topology Change Notification (TCN) to the root bridge. Once the root bridge sees the TCN, it also marks all its BPDUs with the TC flag and floods them back down the tree. Every switch that gets one of these BPDUs then:
- Flushes all dynamic MAC entries on non‑edge ports.
- Starts using a short MAC table aging time (usually 15 seconds).
- We don’t want a server reboot to trigger the topology change process and flush the switches’ MAC address tables.
- We don’t want a server to wait 30 seconds before it can access the network.
What is Portfast?
- A port configured with Portfast skips Listening and Learning states and “jumps” directly to Forwarding. Hence, as soon as the port goes up, the connected device can access the network immediately. (hence the name “PortFast“)
- When a port configured with Portfast goes down and up again, the switch does not send TCN notifications to the root bridge.
How does Portfast work?
- Portfast is configured per switch interface.
- By default, the feature is disabled on all switchports.
- There are two ways to configure Portfast:
- Globally, using the spanning-tree portfast default command in global config mode. It enables Portfast on all access ports. It is recommended in all modern networks.
- Locally, using the spanning-tree portfast in interface config mode. It enables Portfast on a specific interface.
- The feature works only on access ports. The feature is automatically disabled on trunk ports.
- It is strongly recommended that Portfast be configured on all ports that connect to end devices like servers and printers.
- Portfast must not be configured on ports that connect to switches and hubs.
Special Use Cases?
- In some situations, we may want to configure a trunk port with Portfast. That’s why we have the spanning-tree portfast trunk command.
- Trunk ports that connect to devices that do not bridge traffic back to the network can be configured as Portfast trunks.
- The most common examples are trunk links to routers, firewalls, and access points that must connect to multiple VLANs.
- Additionally, trunk links to stub switches can also be configured with Portfast. Such an example is a trunk to a virtual VMWare switch that does not bridge traffic back to the network. Hence, the risk of loops is low.