Site to Site VPN Fortinet
Types Of Virtual Private Networks (VPN)
There are two main types of VPN that people can use to securely connect to corporate networks.
1. Remote access VPN
A remote access VPN enables the user to connect their device to a network from outside their organization’s office. This device-to-network approach typically involves a user connecting their laptop, smartphone, or tablet to a network through their VPN. For organizations with changing IP addresses, dynamic DNS (DDNS) can help maintain consistent VPN connectivity by automatically updating domain names with the correct IP address.
Increasingly, advances in VPN technology enable security checks to be carried out to ensure the device is secure before it is granted permission to connect. Remote access VPNs include cloud VPNs, which enable users to securely access applications and data via their web browser.
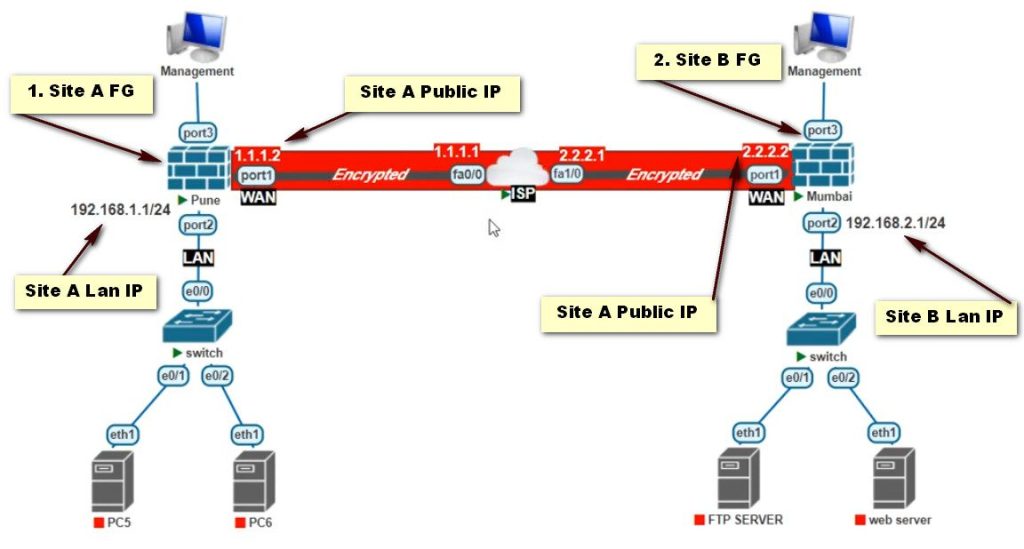
2. Site-to-Site VPN
A site-to-site VPN enables connections between multiple networks. This network-to-network approach is typically used to connect multiple offices or branch locations to a central office. Site-to-site VPN encryption is useful for organizations with several offices based in various geographical locations. It enables them to share resources from a primary network, such as email servers or data storage facilities, across multiple locations. It also allows access to all users as if servers were located in the physical office.
How does a site-to-site VPN work?
A site-to-site VPN creates a secure connection between two or more networks at different locations. It encrypts data transmitted between these networks over the public internet, forming a virtual “tunnel” for secure communication.
What is the function of a site-to-site VPN?
A site-to-site VPN securely connects separate office networks, allowing them to function as one cohesive network. This enables secure communication and resource sharing between different locations, improving collaboration and productivity.
What are the benefits of a site-to-site VPN?
Site-to-site VPNs offer secure communication between geographically dispersed networks, reduced operational costs compared to dedicated leased lines, and centralized network management for improved efficiency.
What are the challenges of a site-to-site VPN?
Challenges include potential performance issues due to latency and bandwidth limitations, complexity in configuration and ongoing management, and ensuring compatibility between different VPN devices and protocols.
What is the difference between site-to-site VPN vs. remote access VPN?
Site-to-site VPNs connect entire networks together, while remote access VPNs connect individual devices, like laptops or smartphones, to a network, often used by employees working remotely.
What is the difference between site-to-site VPN vs. point-to-site VPN?
Site-to-site VPNs connect entire networks, while point-to-site VPNs connect individual devices to a network. Point-to-site offers more granular control over access for individual users and devices.
What is a VPN and what does VPN stand for?
VPN, meaning a virtual private network masks your Internet protocol (IP) address, creating a private connection from a public wi-fi connection.
What does a VPN do and how does it work?
VPNs use virtual connections to create a private network, keeping any device you connect to a public wi-fi safe from hackers and malware, and protecting sensitive information from unauthorized viewing or interception.
What are the advantages of using a VPN?
A VPN masks a user’s true location to the one they set their VPN to. Common uses include; Protecting Browsing History, Hiding your Private Information, Prevent Data Throttling, and Protecting Devices.
Access the FortiGate Admin Interface
- Log into your FortiGate firewall using its web interface. You’ll typically find this at https://<FORTINET_IP>.
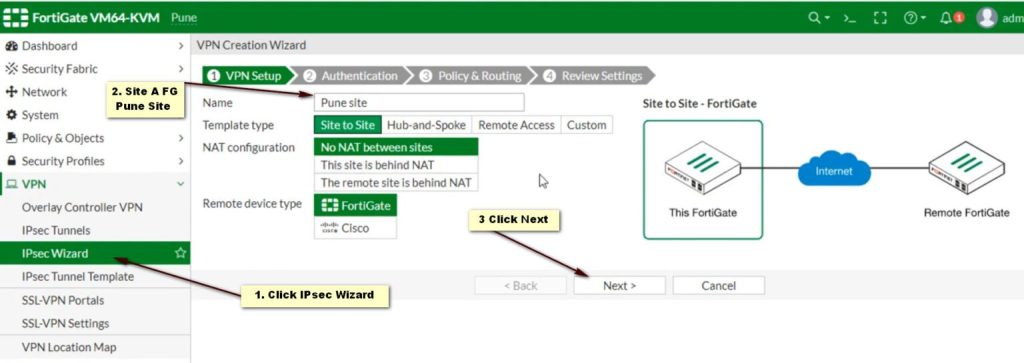
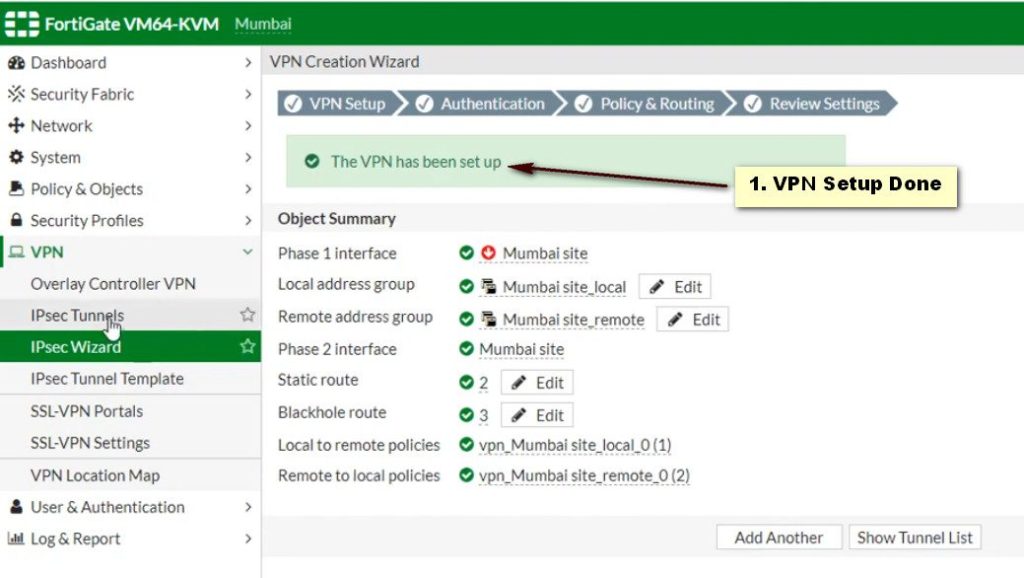
Create a VPN Configuration
- Go to VPN > IPSec Tunnels.
- Click Create New and select Custom.
Phase 1 Configuration
- Name: Enter a name for the tunnel.
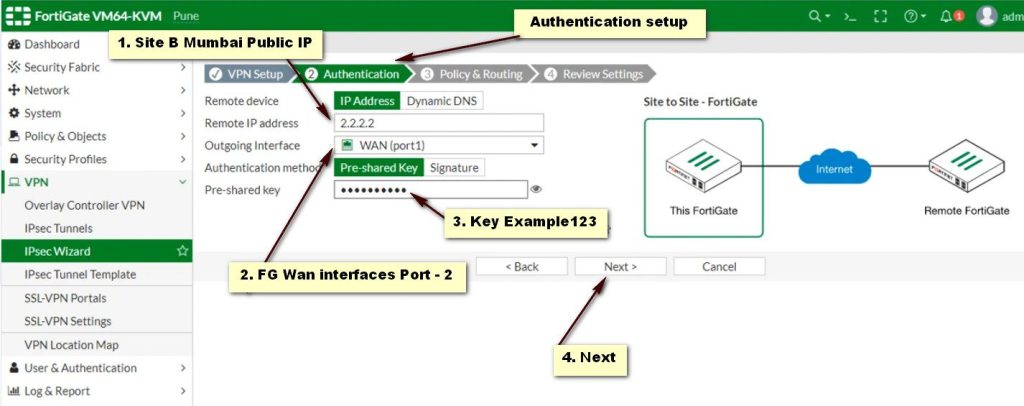
- Remote Gateway: Select Static and enter the StrongSwan public IP.
- Interface: Choose the interface that connects to the internet.
- Mode: Set to Main (Identity Protection).
- Pre-shared Key: Enter the same shared secret used in StrongSwan.
- Encryption and Authentication: Use default settings (AES256, SHA256).
- Advanced Settings: Adjust settings based on your requirements.
Phase 2 Configuration
- Select the tunnel you just created.
- Under Phase 2 Select, click Create.
- Name: Provide a name.
- Local Subnet: Enter the StrongSwan local subnet.
- Remote Subnet: Enter the FortiGate remote subnet.
- Encryption and Authentication: Match the settings used in Phase 1.
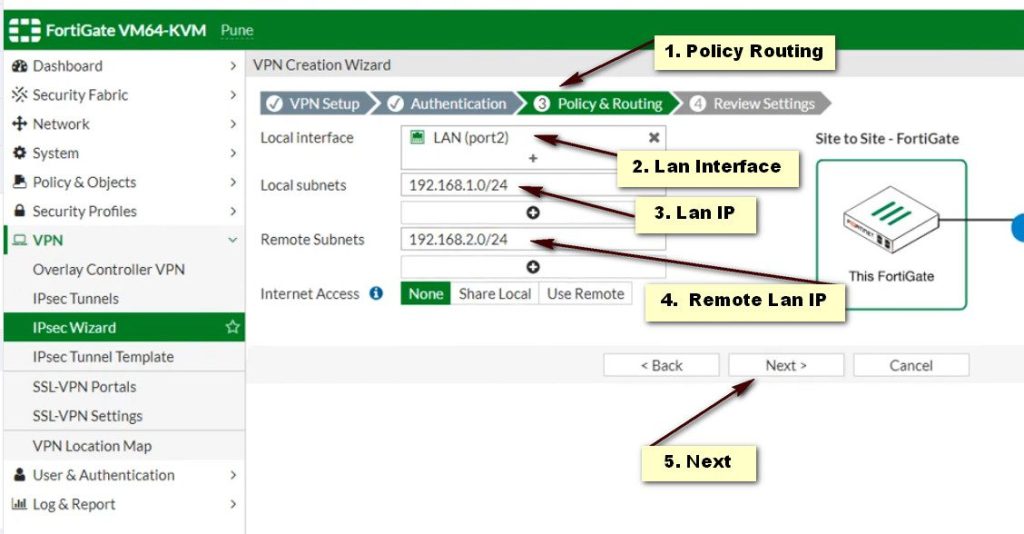
Review Policy Route
- Go to Policy & Objects > IPv4 Policy.
- Create a new policy that allows traffic from the local network to the remote network via the VPN tunnel.
Apply Changes
Save the configuration and apply changes.
