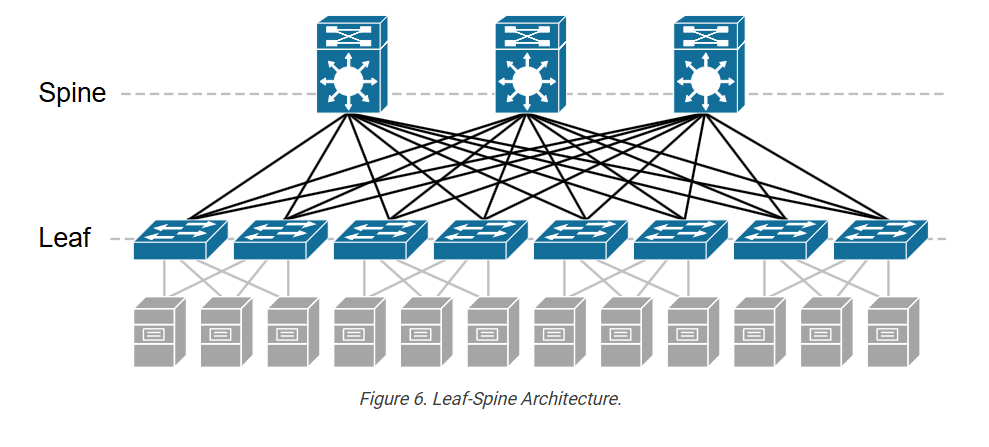
In modern data center networks, Cisco provides a wide range of Nexus series switches that are commonly used for spine–leaf architecture. In this design, leaf switches connect servers and storage, while spine switches act as the high-speed backbone connecting all leaf switches. Below are some commonly used Cisco spine and leaf switch models explained paragraph-wise.
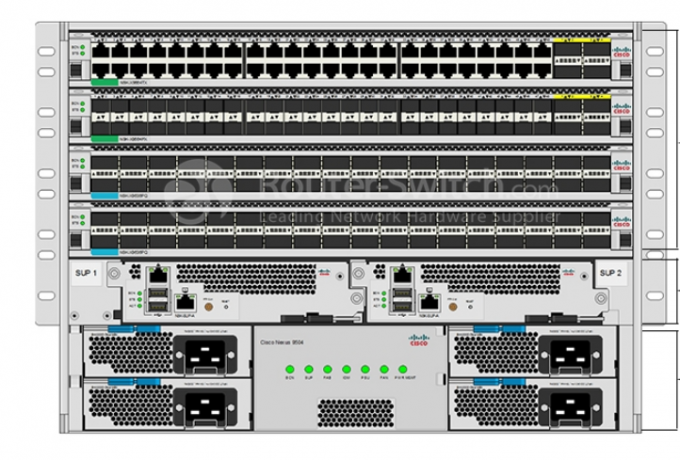
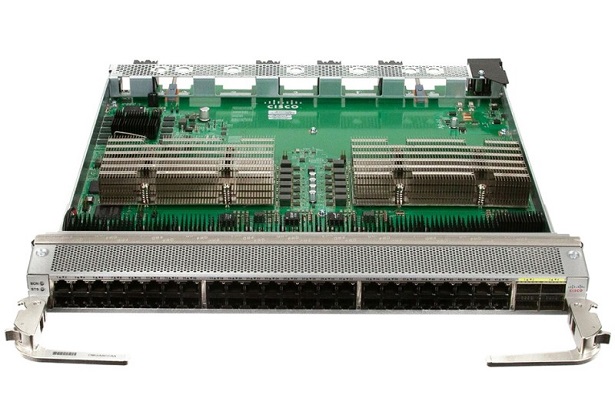
Cisco Nexus 9500 Series (Spine Switch):
The Cisco Nexus 9500 Series is a modular chassis-based switch widely used as a spine or core switch in large data centers. It provides very high port density and supports high-speed interfaces such as 40G, 100G, and 400G Ethernet. Because of its large switching capacity and scalability, it is typically deployed at the spine layer to interconnect many leaf switches and handle large volumes of east-west traffic between servers.
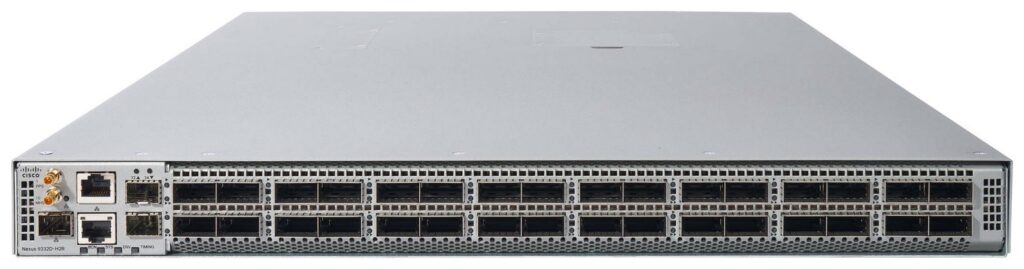
Cisco Nexus 9332C (Spine Switch):
The Cisco Nexus 9332C is a compact fixed switch that offers 32 ports of 100-Gigabit Ethernet. It is often used as a spine switch in medium-sized data center fabrics. This model is suitable for organizations that need high-speed connectivity between leaf switches but do not require a large modular chassis system.
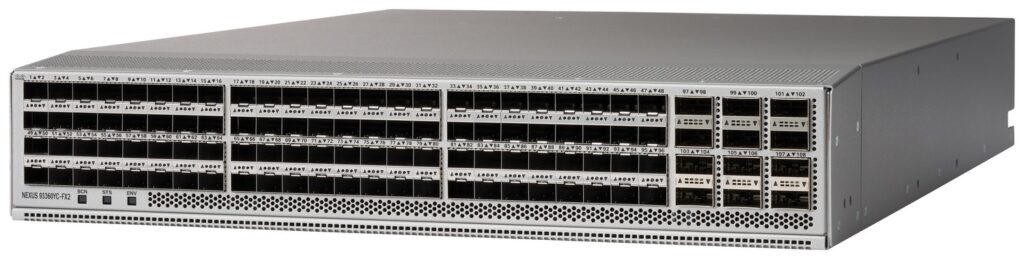
Cisco Nexus 9364C (Spine or Aggregation Switch):
The Cisco Nexus 9364C provides 64 ports of 100-Gigabit Ethernet, making it ideal for high-bandwidth spine-leaf networks. It can operate as a spine switch or aggregation switch, depending on the network design. Its high port density and throughput make it suitable for cloud environments and large enterprise data centers.
Cisco Nexus 93180YC‑FX (Leaf Switch):
The Cisco Nexus 93180YC-FX is a very popular leaf switch used in many enterprise and cloud data centers. It supports 48 ports of 10G/25G Ethernet for server connections and 6 ports of 40G/100G for uplinks to spine switches. This model is typically installed as a Top-of-Rack (ToR) switch, connecting servers in a rack to the spine network.
Cisco Nexus 9372PX (Leaf Switch):
The Cisco Nexus 9372PX is another widely used leaf switch that provides 48 ports of 10-Gigabit Ethernet and 6 ports of 40-Gigabit uplinks. It is commonly deployed in enterprise data centers where servers require reliable 10G connectivity and high-speed uplinks to the spine layer.
Cisco Nexus 93128TX (Leaf Switch):
The Cisco Nexus 93128TX is designed for environments requiring a large number of 10G server connections. It provides 48 ports of 10GBASE-T and multiple 40G uplinks to connect to spine switches. It is frequently used in data centers where many servers use copper Ethernet connections instead of fiber.
Summary:
In Cisco-based data center architecture, spine switches such as the Nexus 9500, 9332C, and 9364C provide the high-speed backbone, while leaf switches like the Nexus 93180YC-FX, 9372PX, and 93128TX connect servers and storage systems. Together, these switches form a scalable and high-performance spine-leaf network fabric used in modern enterprise and cloud data centers.
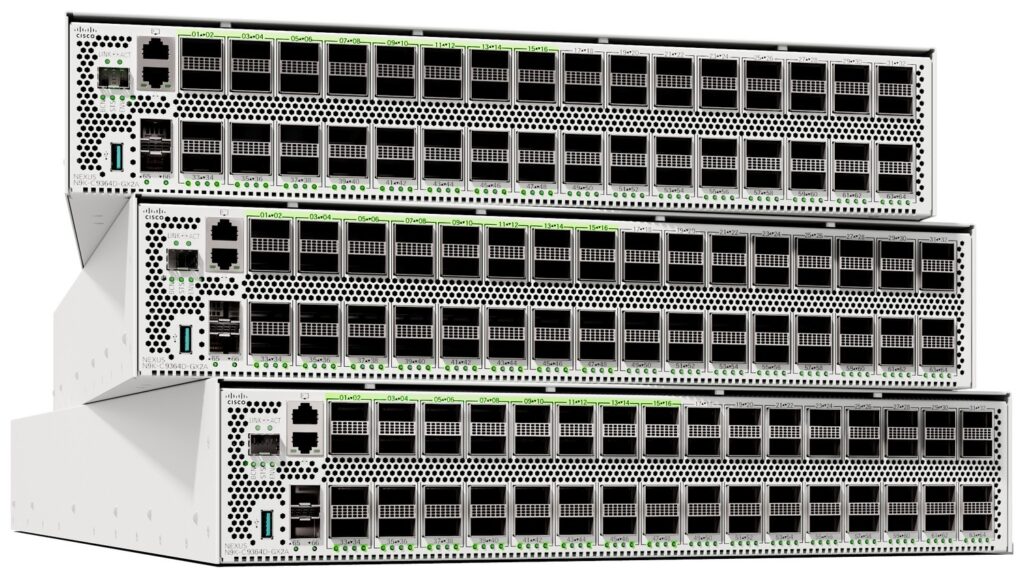
Arista Leaf and Spine Switch Models
Arista 7050X3 Series (Leaf Switch):
The Arista 7050X3 Series is widely used as a leaf switch in cloud and enterprise data centers. It supports 10G, 25G, and 100G Ethernet ports, making it ideal for connecting servers and storage devices. These switches are commonly deployed as Top-of-Rack (ToR) switches in spine-leaf architecture.
Arista 7060X Series (Leaf / Spine Switch):
The Arista 7060X Series can function as either a leaf switch or a small spine switch depending on the network size. It provides high-speed 100G connectivity and is used in scalable data center fabric networks.
Arista 7500R Series (Spine Switch):
The Arista 7500R Series is a modular spine/core switch used in large hyperscale and cloud data centers. It offers very high port density and large switching capacity to handle heavy east-west traffic between servers.
Huawei Leaf and Spine Switch Models
Huawei CloudEngine 6850 Series (Leaf Switch):
The Huawei CloudEngine 6850 Series is commonly used as a leaf switch in enterprise data centers. It provides 25G server ports and 100G uplinks to connect to spine switches.
Huawei CloudEngine 8850 Series (Spine Switch):
The Huawei CloudEngine 8850 Series is designed as a spine switch in large data center fabrics. It supports high-bandwidth 100G connectivity and provides low latency for data center traffic.
Huawei CloudEngine 16800 Series (Core / Spine Switch):
The Huawei CloudEngine 16800 Series is a high-end modular switch used as a core or spine device in large enterprise and telecom data centers.
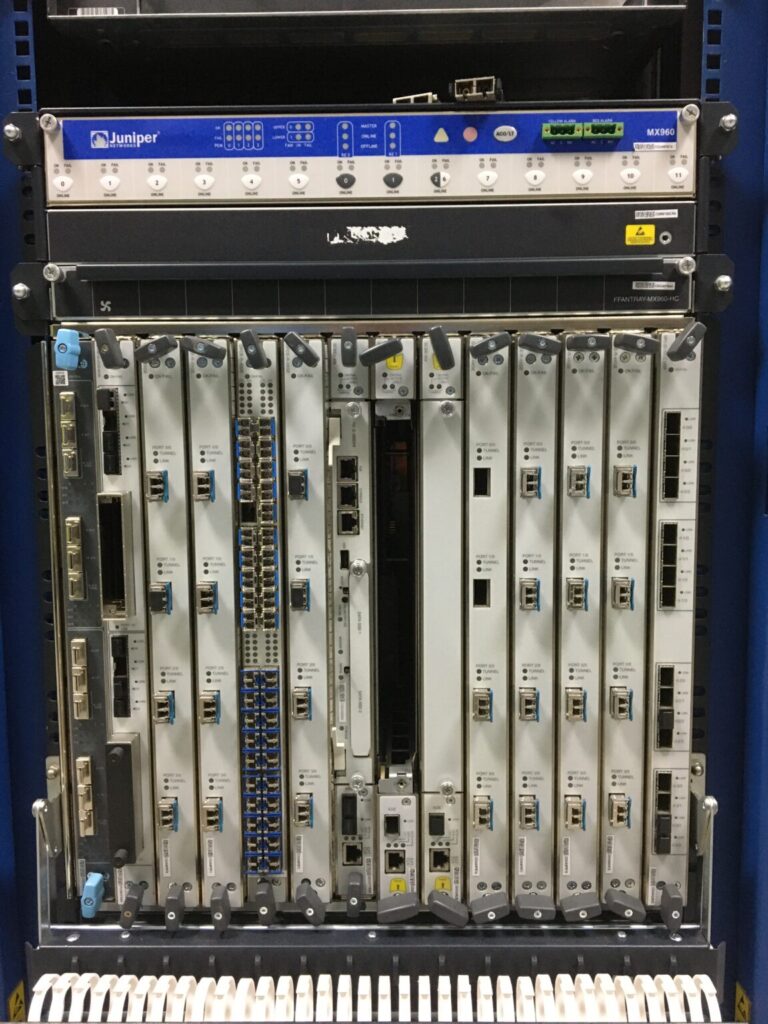
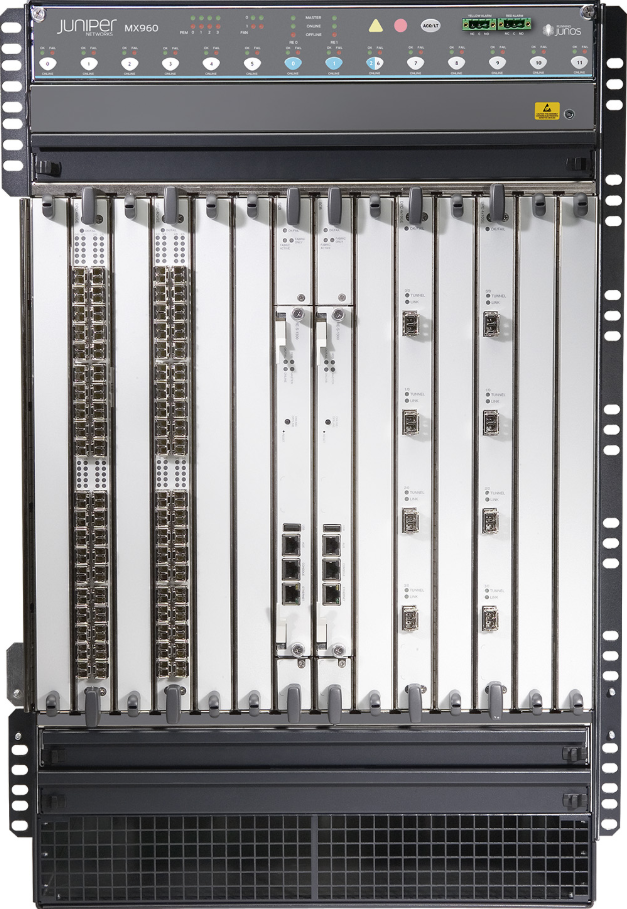
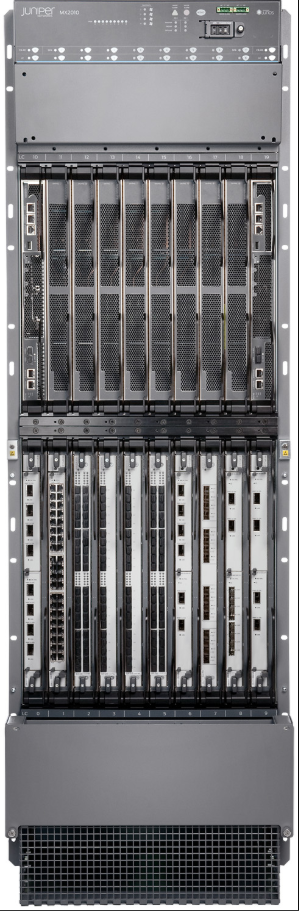
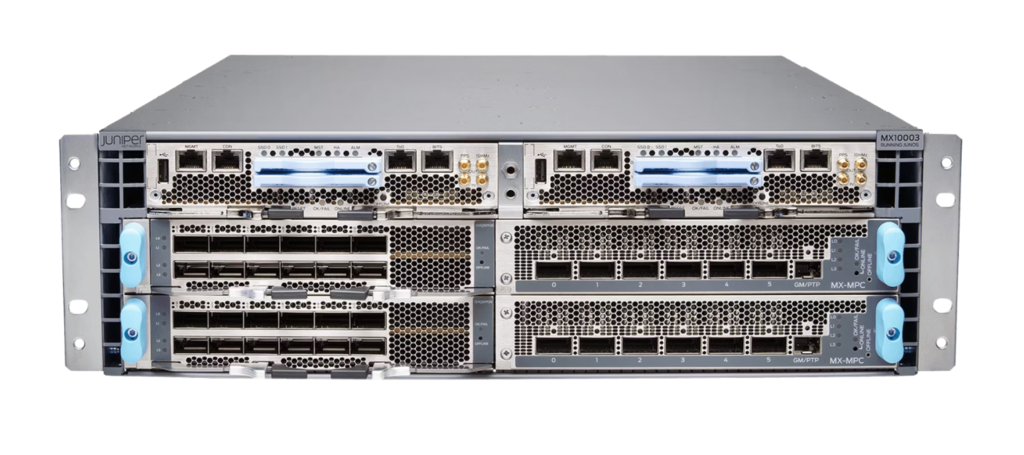
Juniper Leaf and Spine Switch Models
Juniper QFX5120 Switch (Leaf Switch):
The Juniper QFX5120 is commonly deployed as a leaf switch in data center fabric architecture. It supports 10G/25G server connectivity and 100G uplinks to spine switches.
Juniper QFX5200 Switch (Leaf / Spine Switch):
The Juniper QFX5200 can operate as either a leaf switch or small spine switch in data center networks. It provides high-performance 100G Ethernet ports.
Juniper QFX10008 (Spine Switch):
The Juniper QFX10008 is a modular spine switch designed for large-scale data center fabrics. It offers very high switching capacity and large port density for connecting many leaf switches.
1. Cisco Data Center Spine / Core Switch Models
| Model | Purpose |
|---|
| Cisco Nexus 9500 Series | Modular core/spine switch used in large enterprise and cloud data centers. |
| Cisco Nexus 9332C | Fixed 32×100G spine switch used in spine-leaf fabric networks. |
| Cisco Nexus 9364C | Used as spine or aggregation switch with high-speed 100G ports. |
| Cisco Nexus 92300YC Series | Flexible switch that can work as leaf or spine in modern data centers. |