SSL Deep Inspection & Intrusion Prevention
SSL Deep Inspection
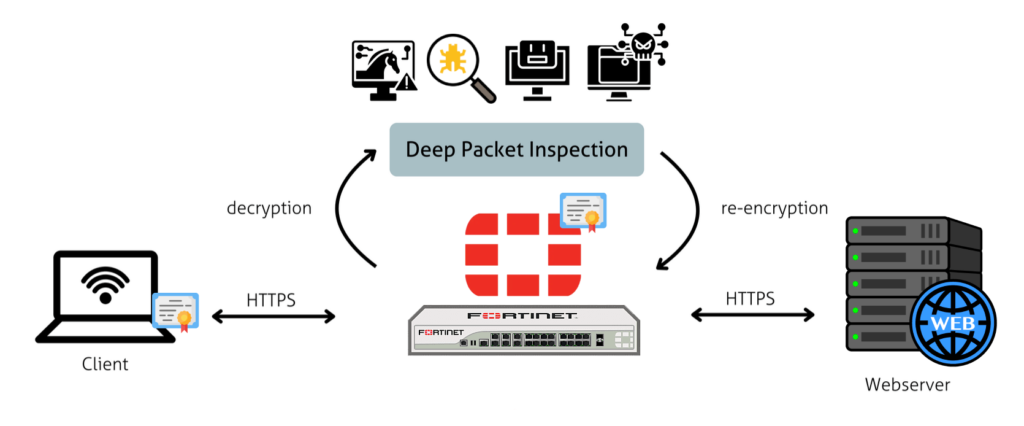
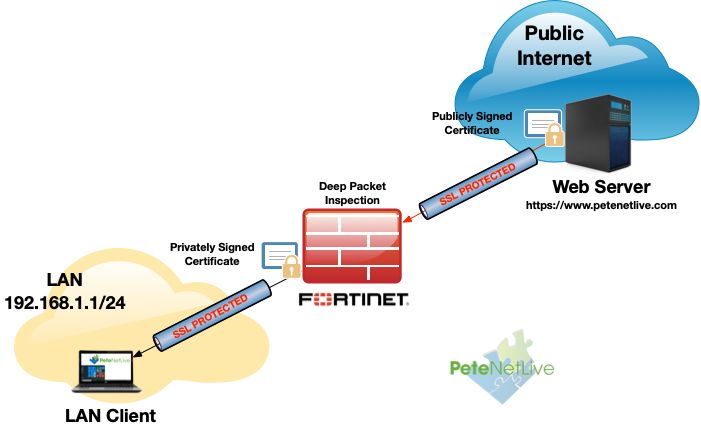
SSL Deep Inspection is a firewall security feature that decrypts, inspects, and analyzes encrypted HTTPS traffic (SSL/TLS traffic) to detect hidden threats such as malware, phishing, or data leaks.
Normally, most internet traffic today is encrypted using SSL/TLS (shown as HTTPS), which makes it secure. However, attackers can also hide viruses or malicious content inside encrypted traffic. SSL Deep Inspection solves this problem by temporarily decrypting the traffic, checking it, and then re-encrypting it before sending it to the user.
When a user visits an HTTPS website, the firewall acts like a middle layer. It decrypts the data, scans it for threats using security rules, and then allows or blocks the content based on the result. This ensures that even encrypted traffic is not used to bypass security.
Example
In an office network, an employee tries to download a file from an HTTPS website. The firewall performs SSL inspection, detects that the file contains malware, and blocks it before it reaches the system.
In another case, if a phishing website uses HTTPS to look safe, SSL Deep Inspection can still detect and block it.
Importance
SSL Deep Inspection is important because:
- Most modern websites use HTTPS encryption
- Hackers hide malware inside encrypted traffic
- Basic firewalls cannot see encrypted data
- It improves overall network security
In advanced firewalls like Fortinet FortiGate, SSL Deep Inspection is used to inspect encrypted web traffic, detect hidden threats, and enforce security policies effectively.
Why Need SSL Deep Inspection
SSL Deep Inspection is needed because most of today’s internet traffic is encrypted using SSL/TLS (HTTPS). While encryption protects data from outsiders, it also creates a security blind spot for traditional firewalls because they cannot see what is inside the encrypted traffic.
- Attackers take advantage of this by hiding malware, ransomware, phishing pages, and data theft activities inside HTTPS connections. Without inspection, these threats can easily bypass normal security filters and enter the network without detection.
- SSL Deep Inspection solves this problem by decrypting the traffic, scanning it for malicious content, applying security policies, and then re-encrypting it before sending it to the user. This allows the firewall to maintain security even in encrypted communication.
- It is also needed to prevent data leakage. Employees or users may unknowingly upload sensitive information through encrypted channels to unauthorized websites or cloud services. SSL inspection helps detect and control such activities.
- In organizations like offices, banks, and schools, SSL Deep Inspection is important because it ensures that even secure websites are not used as a medium for cyberattacks or unauthorized data transfer.
In advanced firewalls such as Fortinet FortiGate, SSL Deep Inspection is a key feature used to inspect HTTPS traffic, block hidden threats, and enforce strong security policies across the network.
SSL Deep Inspection – Example
Example 1: Malware hidden in HTTPS download (Office network)
An employee tries to download a software tool from a website that uses HTTPS (secure connection). Since the connection is encrypted, a normal firewall cannot see inside it.
However, with SSL Deep Inspection enabled, the firewall:
- Decrypts the HTTPS traffic
- Scans the downloaded file
- Detects that the file contains a Trojan virus
- Blocks the download immediately
- Re-encrypts safe traffic and sends it to the user
So, even though the website looked secure, the threat is stopped before entering the system.
Example 2: Phishing website using HTTPS
A user receives a link that looks like a bank login page (example: fake banking site). The site uses HTTPS to appear safe.
Without SSL inspection, the firewall may allow it because it is encrypted.
With SSL Deep Inspection:
- Firewall decrypts the website content
- Detects it is a phishing page (fake login form)
- Blocks access and warns the user
This prevents theft of login credentials like passwords and OTPs.
Example 3: Data leakage in organization
An employee tries to upload confidential company files to a personal cloud storage website using HTTPS.
With SSL Deep Inspection:
- Firewall decrypts upload traffic
- Detects sensitive company data
- Blocks the upload based on security policy
- Logs the activity for admin review
This helps prevent data theft or leakage.
In real firewall systems
In advanced firewalls like Fortinet FortiGate, SSL Deep Inspection is widely used to:
- Inspect encrypted web traffic (HTTPS)
- Detect malware hidden inside secure connections
- Block phishing and fake websites
- Control data transfer securely
Intrusion Prevention System (IPS)
1. Introduction
An Intrusion Prevention System (IPS) in Fortinet is a security feature that monitors network traffic and detects and blocks malicious activities in real time. It is built into Fortinet security products, mainly the FortiGate firewall, to protect networks from cyber threats like hacking attempts, malware, and exploits.
2. Working of Fortinet IPS
Fortinet IPS continuously inspects data packets flowing in and out of the network. It compares this traffic with a database of known attack signatures and suspicious behavior patterns. If any threat is detected, it immediately takes action such as blocking the traffic, resetting the connection, or alerting the administrator.
3. Features of Fortinet IPS
Fortinet IPS provides features like signature-based detection, anomaly detection, real-time blocking, and automatic updates of threat intelligence. It also uses FortiGuard Labs threat intelligence to stay updated with the latest cyber threats worldwide.
4. Example of IPS in action
For example, if a hacker tries to exploit a vulnerability in a company’s server or inject malware through network traffic, Fortinet IPS will detect the attack pattern and stop it instantly before it reaches the system, preventing damage.
5. Importance of Fortinet IPS
Fortinet IPS is important because it provides proactive protection, meaning it stops attacks before they succeed. It helps organizations secure sensitive data, maintain network performance, and reduce risks from cyber threats.
Why We Need Intrusion Prevention System (IPS)
Why we need Intrusion Prevention System (IPS)
An Intrusion Prevention System (IPS) is needed to protect computer networks from cyber threats by detecting and automatically blocking malicious activities in real time.
1. Protection from cyberattacks
IPS helps stop attacks like hacking attempts, malware, ransomware, port scanning, and denial-of-service (DoS) attacks before they enter the system.
2. Real-time blocking of threats
Unlike systems that only detect and alert, IPS can immediately block harmful traffic, preventing damage at the source.
3. Prevent data theft and unauthorized access
IPS protects sensitive information such as user data, financial records, and company files by stopping unauthorized attempts to access them.
4. Early detection of suspicious activity
It monitors network traffic and identifies unusual behavior like repeated login failures or scanning of multiple ports, which may indicate an attack.
5. Reduces downtime and damage
By stopping attacks early, IPS helps avoid system crashes, service disruption, and costly recovery operations.
6. Strengthens overall security
IPS works with firewalls and antivirus systems to provide multi-layered network protection, making the system more secure.
Simple example
If a hacker tries to scan open ports or exploit a server vulnerability, the IPS will detect the activity and block it instantly before any harm is done.
Example of Intrusion Prevention System (IPS)
Example of Intrusion Prevention System (IPS)
Example 1: Port scanning attack
A hacker uses a tool like Nmap to scan a company’s server and checks multiple ports (like 22, 80, 443) to find open services.
👉 The IPS detects this unusual pattern of repeated port requests and blocks the hacker’s IP address immediately, stopping further scanning.
Example 2: Malware injection attempt
A user tries to send a malicious file through the network that matches a known virus signature.
👉 The IPS identifies the file as malware and blocks it before it reaches the system.
Example 3: Brute-force login attack
A hacker repeatedly tries different passwords to access a server.
👉 The IPS notices too many failed login attempts and automatically blocks that IP address.
Simple summary
IPS works like a security guard that watches network traffic and stops suspicious activity instantly before it can harm the system.
